Manage access to a workspace in Microsoft Playwright Testing Preview
In this article, you learn how to manage access to a workspace in Microsoft Playwright Testing Preview. The service uses Azure role-based access control (Azure RBAC) to authorize access rights to your workspace. Role assignments are the way you control access to resources using Azure RBAC.
Important
Microsoft Playwright Testing is currently in preview. For legal terms that apply to Azure features that are in beta, in preview, or otherwise not yet released into general availability, see the Supplemental Terms of Use for Microsoft Azure Previews.
Prerequisites
To assign roles in Azure, your account needs the User Access Administrator, Owner, or one of the classic administrator roles.
To verify your permissions in the Azure portal:
- In the Azure portal, go to your Microsoft Playwright Testing workspace.
- On the left pane, select Access Control (IAM), and then select View my access.
Default roles
Microsoft Playwright Testing workspaces uses three Azure built-in roles. To grant users access to a workspace, you assign them one of the following Azure built-in roles:
| Role | Access level |
|---|---|
| Reader | - Read-only access to the workspace in the Playwright portal. - View test results for the workspace. - Can't create or delete workspace access tokens. Can't run Playwright tests on the service. |
| Contributor | - Full access to manage the workspace in the Azure portal but can't assign roles in Azure RBAC. - Full access to the workspace in the Playwright portal. - Create and delete their access tokens. - Run Playwright tests on the service. |
| Owner | - Full access to manage the workspace in the Azure portal, including assigning roles in Azure RBAC. - Full access to the workspace in the Playwright portal. - Create and delete their access tokens. - Run Playwright tests on the service. |
Important
Before you assign an Azure RBAC role, determine the scope of access that is needed. Best practices dictate that it's always best to grant only the narrowest possible scope. Azure RBAC roles defined at a broader scope are inherited by the resources beneath them. For more information about scope for Azure RBAC role assignments, see Understand scope for Azure RBAC.
Grant access to a user
You can grant a user access to a Microsoft Playwright Testing workspace by using the Azure portal:
Sign in to the Playwright portal with your Azure account.
Select the workspace settings icon, and then go to the Users page.
Select Manage users for your workspace in the Azure portal to go to your workspace in the Azure portal.
Alternately, you can go directly to the Azure portal and select your workspace:
- Sign in to the Azure portal.
- Enter Playwright Testing in the search box, and then select Playwright Testing in the Services category.
- Select your Microsoft Playwright Testing workspace from the list.
- On the left pane, select Access Control (IAM).
On the Access Control (IAM) page, select Add > Add role assignment.
If you don't have permissions to assign roles, the Add role assignment option is disabled.
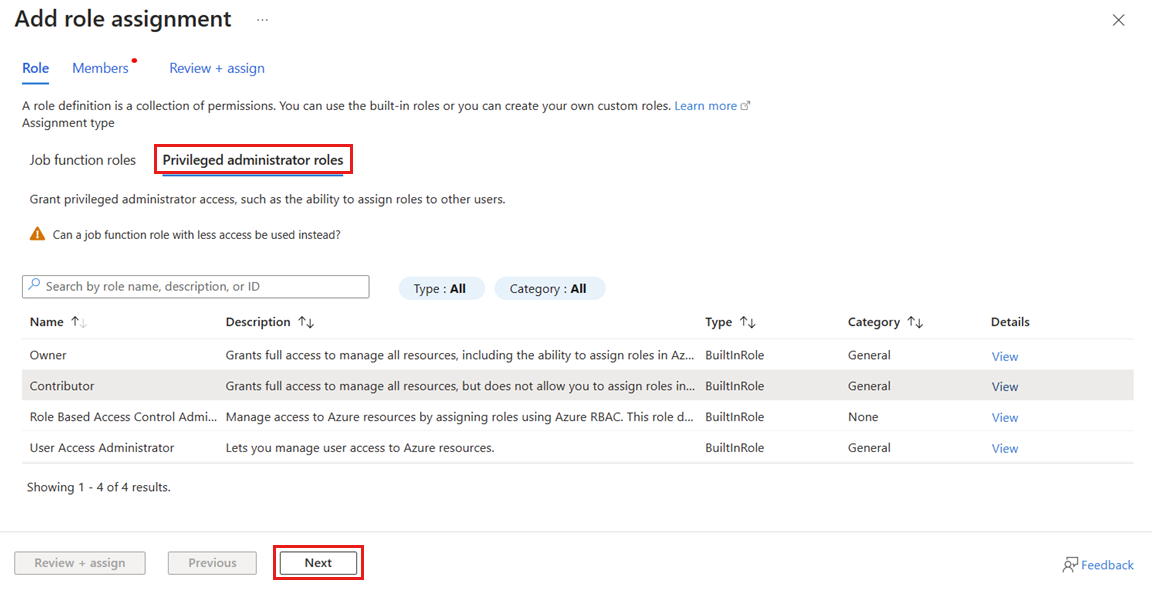
On the Role tab, select Privileged administrator roles.
Select one of the Microsoft Playwright Testing default roles, and then select Next.
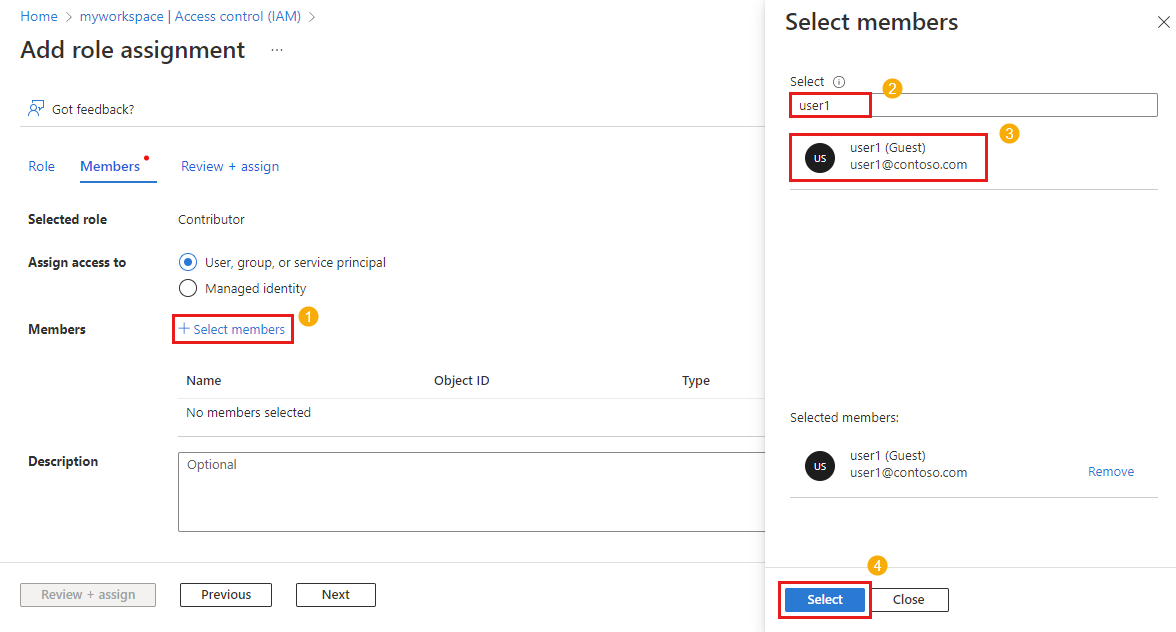
On the Members tab, make sure User, group, or service principal is selected.
Select Select members, find and select the users, groups, or service principals.
Select Review + assign to assign the role.
For more information about how to assign roles, see Assign Azure roles using the Azure portal.
Revoke access for a user
You can revoke a user's access to a Microsoft Playwright Testing workspace using the Azure portal:
In the Azure portal, go to your Microsoft Playwright Testing workspace.
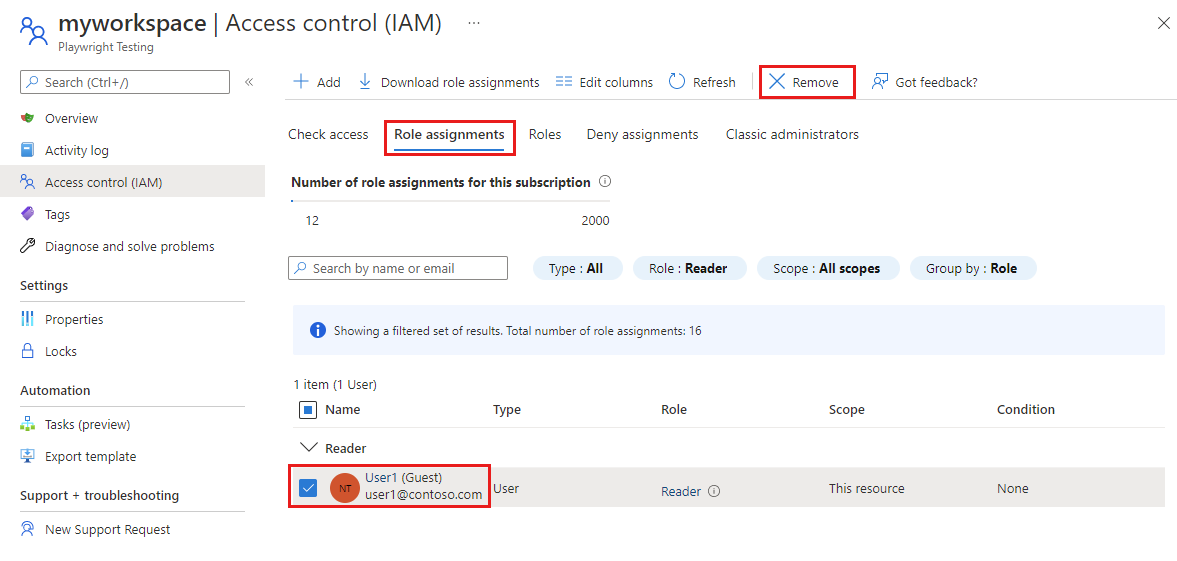
On the left pane, select Access Control (IAM), and then select Role assignments.
In the list of role assignments, add a checkmark next to the user and role you want to remove, and then select Remove.
Select Yes in the confirmation window to remove the role assignment.
For more information about how to remove role assignments, see Remove Azure role assignments.
(Optional) Use Microsoft Entra security groups to manage workspace access
Instead of granting or revoking access to individual users, you can manage access for groups of users using Microsoft Entra security groups. This approach has the following benefits:
- Avoid the need for granting team or project leaders the Owner role on the workspace. You can grant them access only to the security group to let them manage access to the workspace.
- You can organize, manage and revoke users' permissions on a workspace and other resources as a group, without having to manage permissions on a user-by-user basis.
- Using Microsoft Entra groups helps you to avoid reaching the subscription limit on role assignments.
To use Microsoft Entra security groups:
Add a group owner. This user has permissions to add or remove group members. The group owner isn't required to be group member, or have direct RBAC role on the workspace.
Assign the group an RBAC role on the workspace, such as Reader or Contributor.
Add group members. The added members can now access to the workspace.
Create a custom role for restricted tenants
If you're using Microsoft Entra tenant restrictions and users with temporary access, you can create a custom role in Azure RBAC to manage permissions and grant access to run tests.
Perform the following steps to manage permissions with a custom role:
Follow these steps to create an Azure custom role.
Select Add permissions, and enter Playwright in the search box, and then select Microsoft.AzurePlaywrightService.
Select the
microsoft.playwrightservice/accounts/writepermission, and then select Add.Follow these steps to add a role assignment for the custom role to the user account.
The user can now continue to run tests in the workspace.
Troubleshooting
Here are a few things to be aware of while you use Azure role-based access control (Azure RBAC):
When you create a resource in Azure, such as a workspace, you are not automatically the owner of the resource. Your role is inherited from the highest scope role that you're authorized against in that subscription. As an example, if you're a Contributor for the subscription, you have the permissions to create a Microsoft Playwright Testing workspace. However, you would be assigned the Contributor role against that workspace, and not the Owner role.
When there are two role assignments to the same Microsoft Entra user with conflicting sections of Actions/NotActions, your operations listed in NotActions from one role might not take effect if they're also listed as Actions in another role. To learn more about how Azure parses role assignments, read How Azure RBAC determines if a user has access to a resource.
It can sometimes take up to 1 hour for your new role assignments to take effect over cached permissions.
Related content
Get started with running Playwright tests at scale
Learn how to manage Playwright Testing workspaces