@Albertk
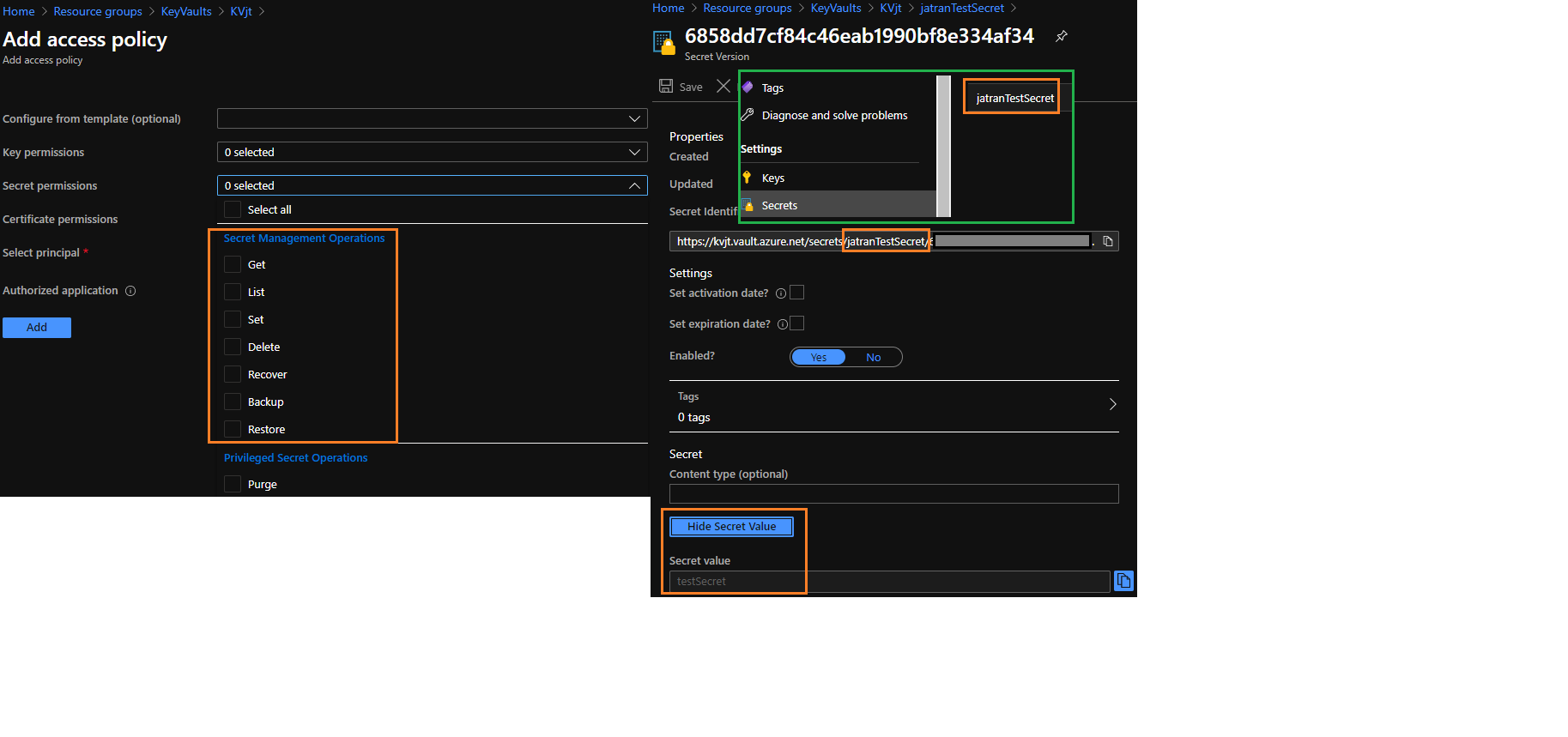
Access to the Azure Key Vault requires proper authentication and authorization before a caller (user or application) can get access. Even if a user retrieved the secret name within your Docker-Compose file, the 'true value' of that secret would still be hidden and secured within the Key Vault, because the secret name is different from the actual value of a secret.
If you're worried about access control or loss of secret information, you can easily mitigate these issues by using Azure RBAC, which will let you control access to resources such as the Key Vault and keys/secrets within the vault.
Access policies is another way to secure your keys/secrets, since you can assign your WebApp certain permissions within the vault when it comes to get, set, list, delete, etc.
Lastly, I was able to find a tutorial on how to use Key Vault references within an ASP.NET Core app, which might be what you're looking for.
I hope this helps! If you have any other questions, please let me know.
Thank you for your time and patience!
