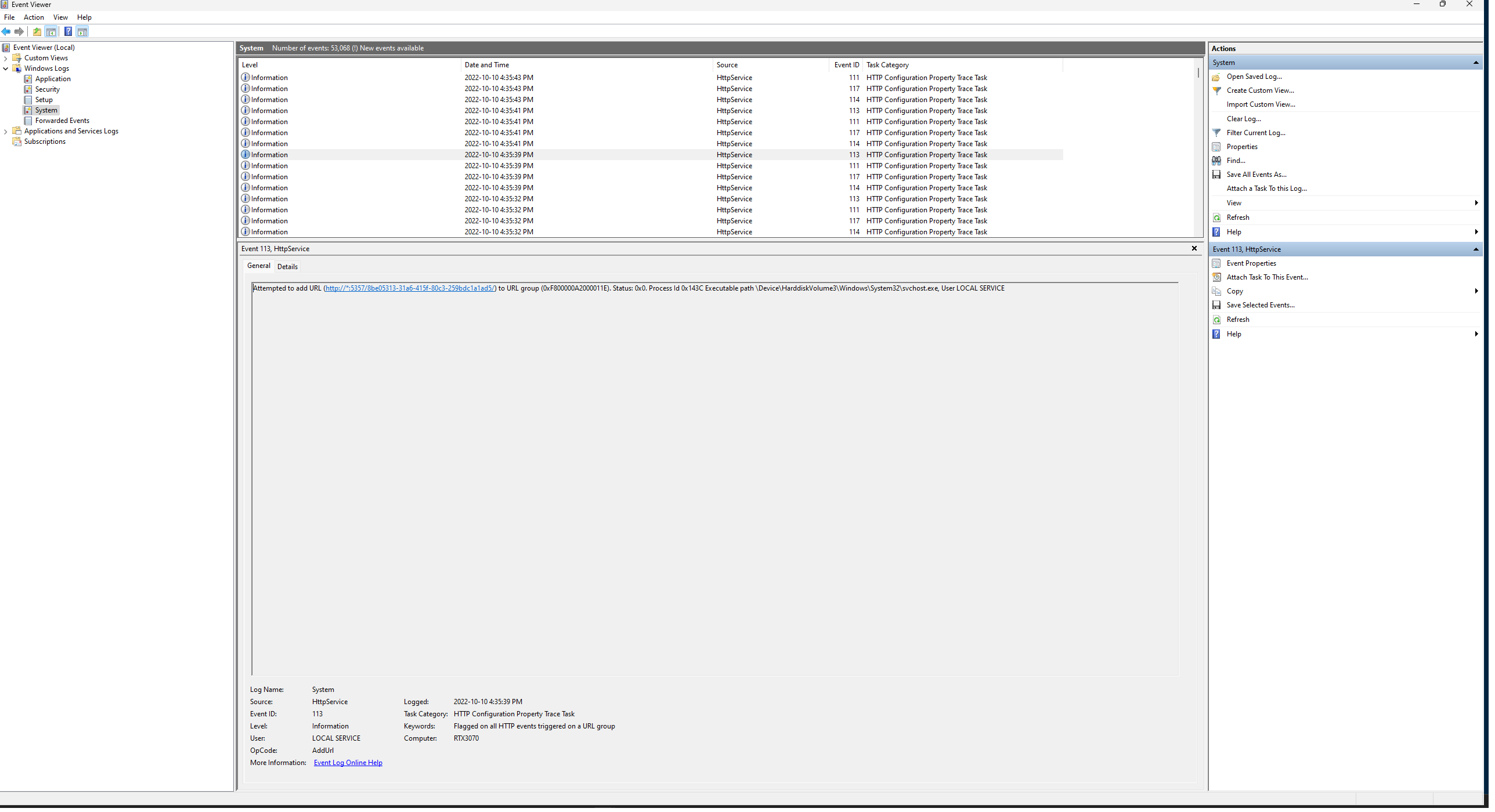
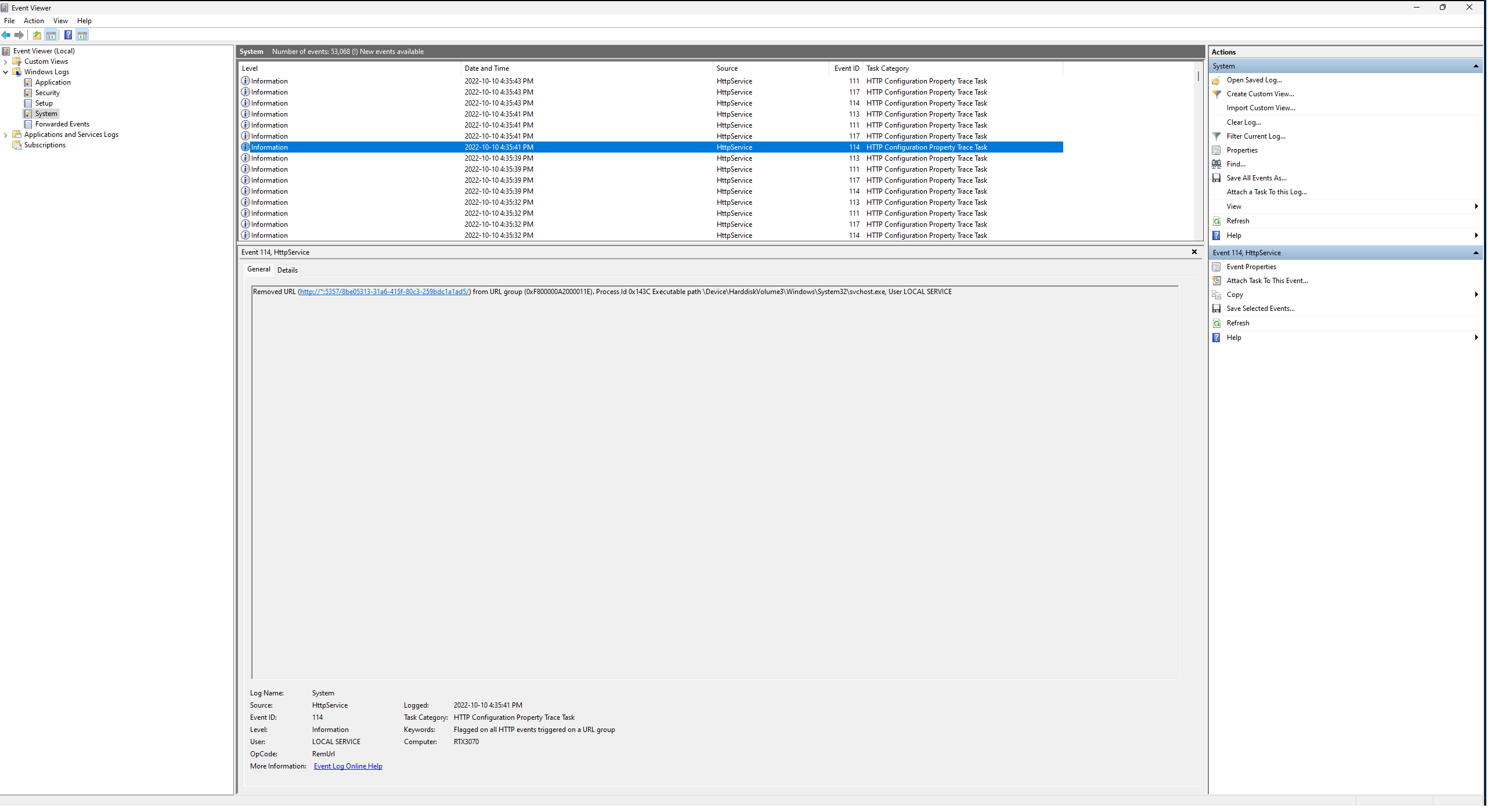
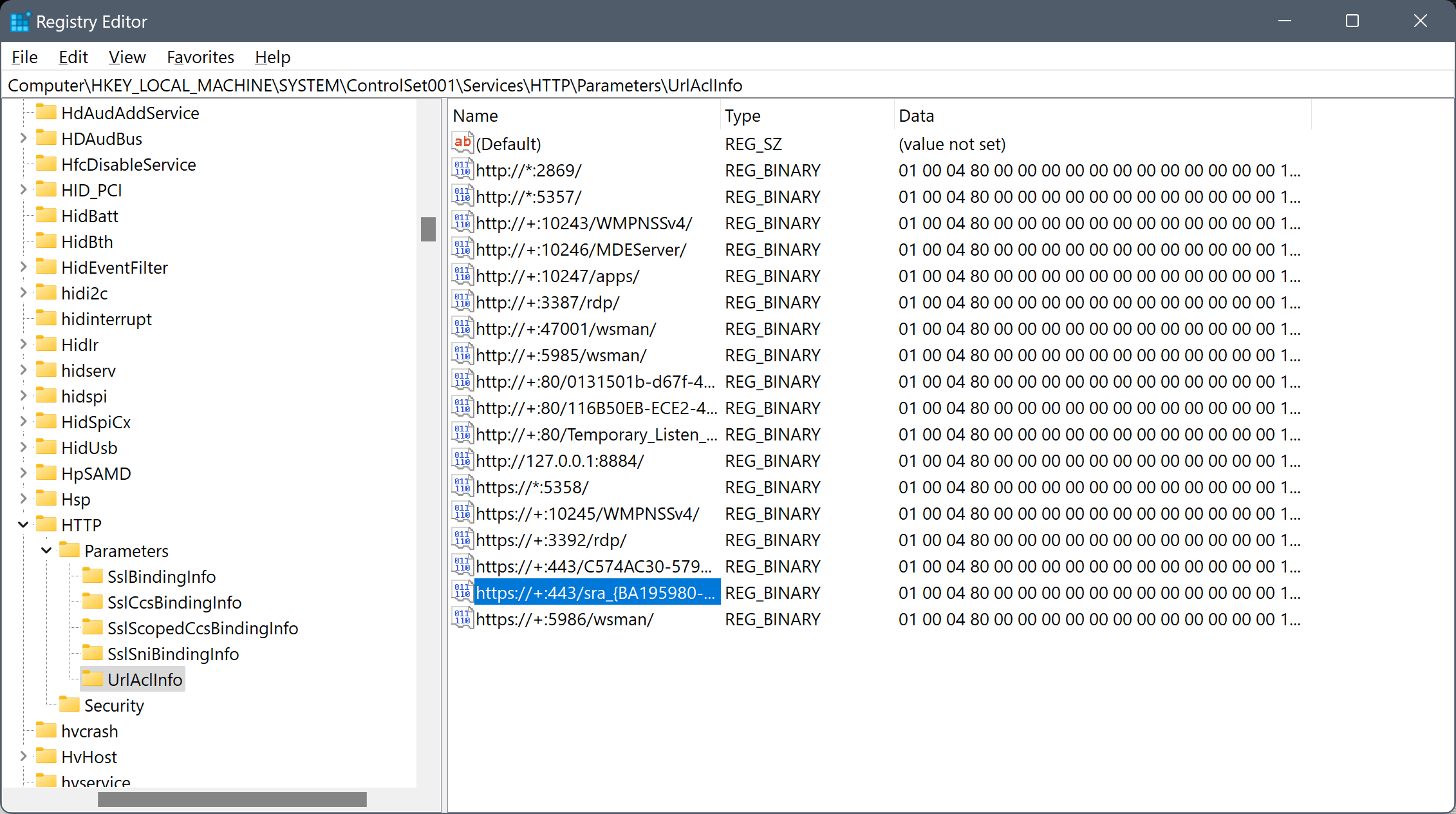
Searching the registry for a GUID found in an associated HttpService 112 event's details tab in Event Viewer revealed a key containing URLs corresponding to each of the HttpService Event Log entries. Since this key is within the Services folder/key:
HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\HTTP\Parameters\UrlAclInfo
it would then seem as if the offending service is HttpService itself. However, what processes/services registered these URLs are most likely at the root of the cause. The process/service names that appear within the URLs are clear indicators (rdp, wsman, apps, MDEServer, ...). I suppose that it could've registered a few for itself, possibly for utilitarian purposes.
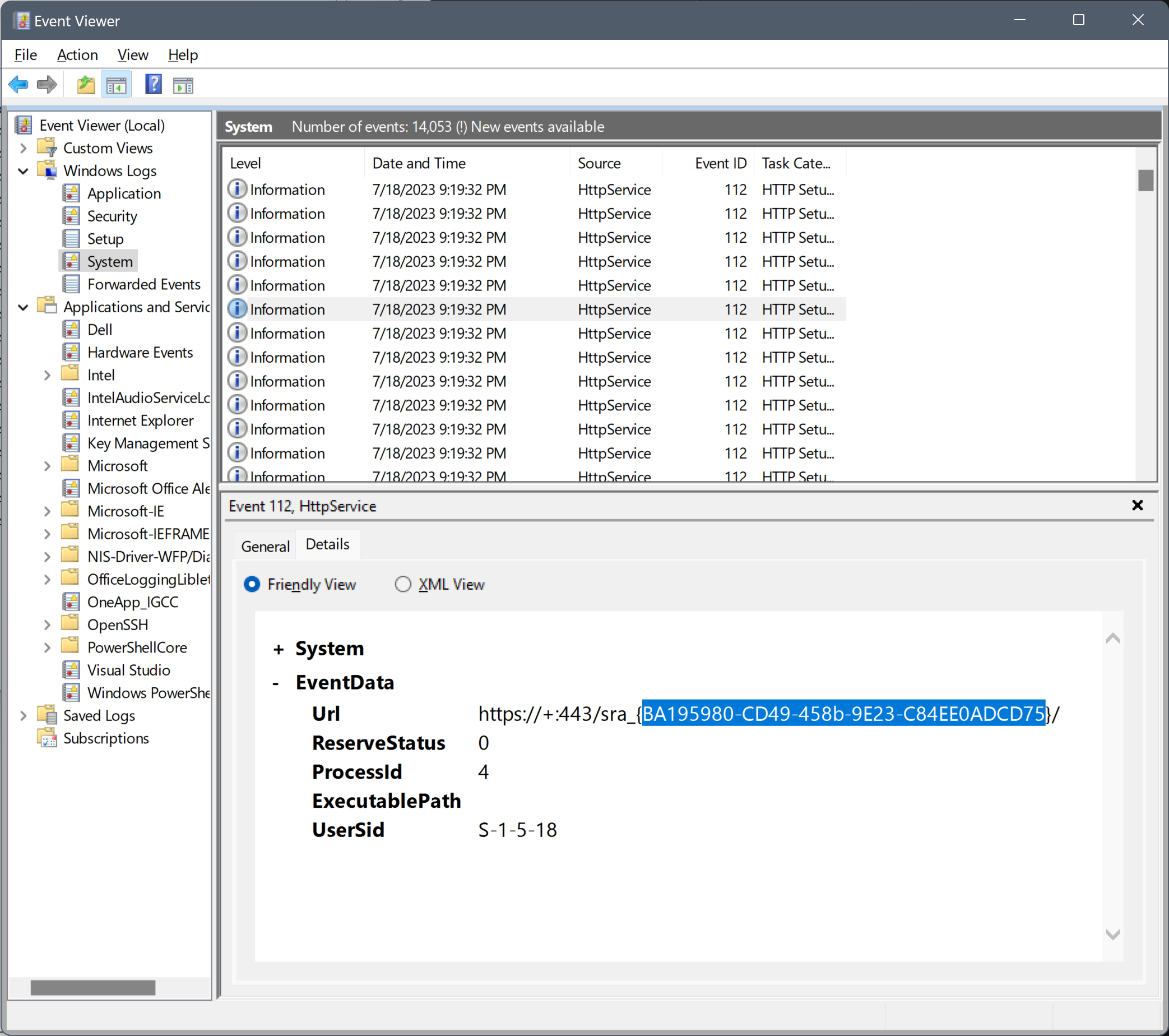
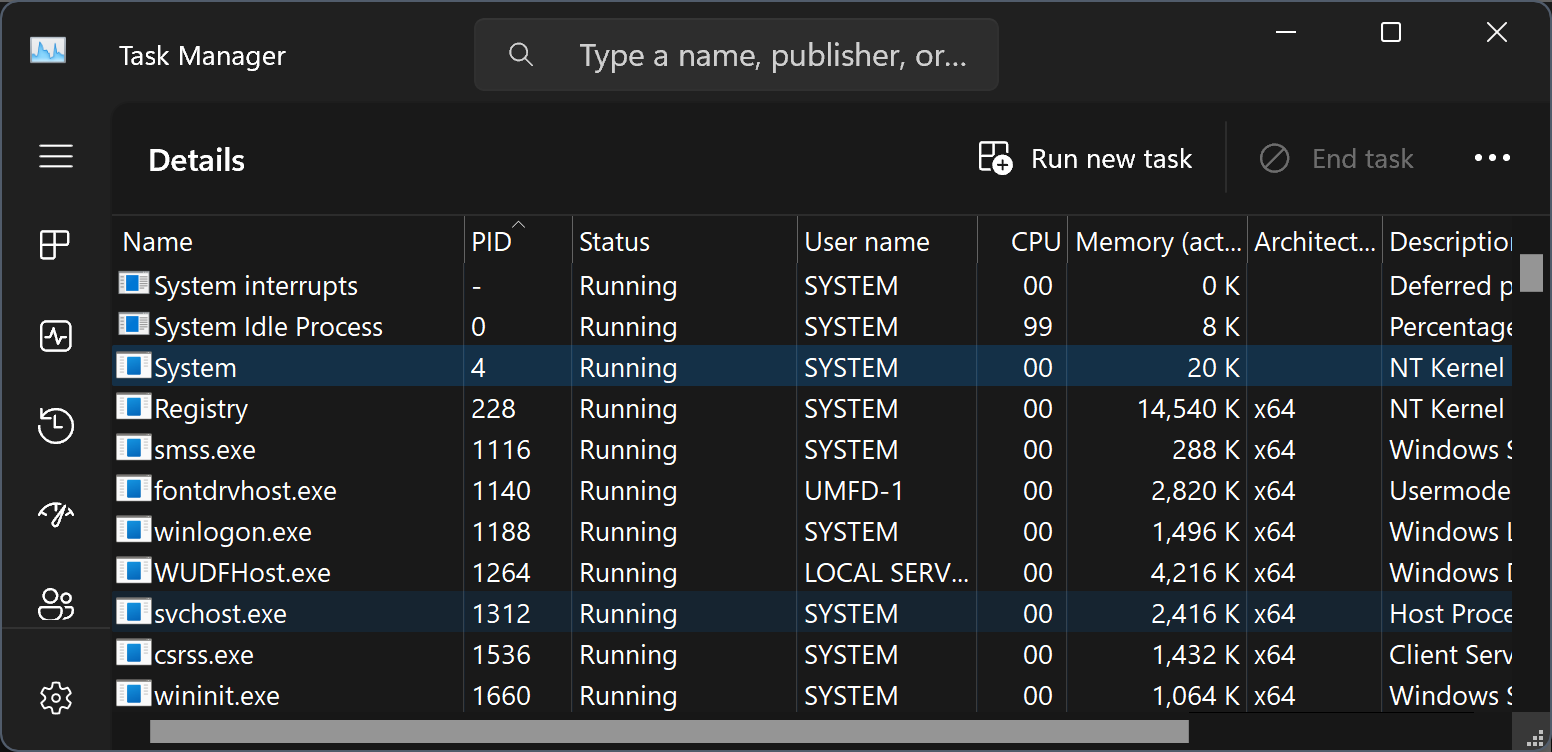
Note also that ProcessId 4 corresponds to the kernel system process: