@SwathiDhanwada-MSFT Thanks. I have fill the support request for the same.
Azure Custom policy - Non-Compliance warning not showing for audit policy.
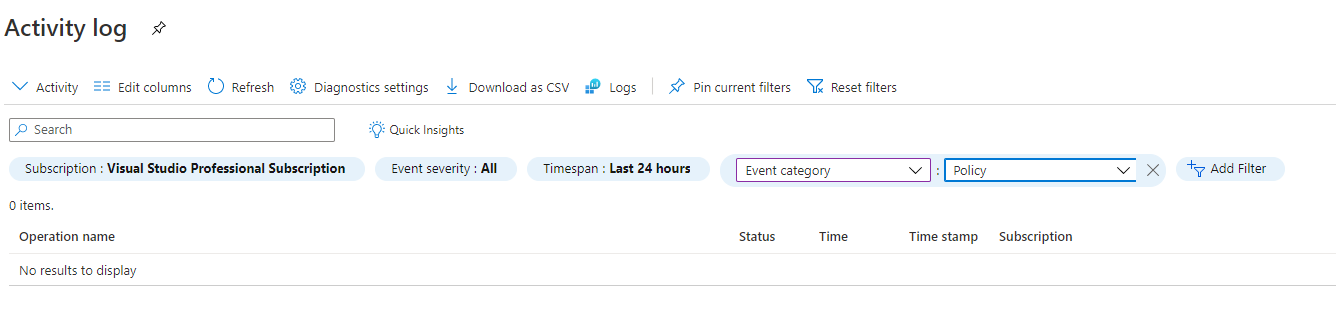
I have create simple Azure custom policy to check tags is exist or not, and assigned it to subscription level. It is showing the non compliances resources and resource group on policy blade as expected. But when I check on activity log, it is not listing any log for operation policy audit check.
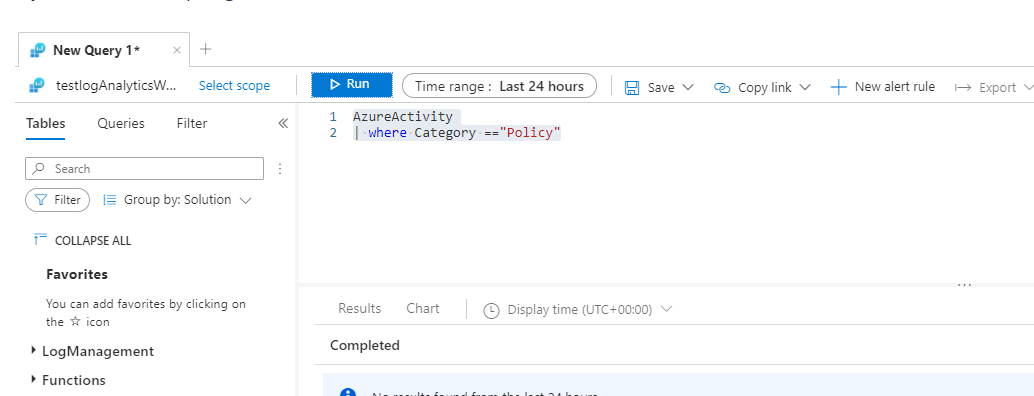
Also, I have send activity logs into Log analytic but no luck.
2 answers
Sort by: Most helpful
-
-
SwathiDhanwada-MSFT 18,756 Reputation points
2021-01-25T04:51:14.53+00:00 Thanks @Kiran Kolte for sharing support case number. Sharing the resolution for the benefit of broader community.
AzureActivity command which is stored in the AzureActivity table, follows the instructions from this documentation. Microsoft Technical Support team noticed that when the Resource Group becomes non-complaint it does not log in the Activity Log. This happens because there are two types of operations that occurs in policies, Greenfield operations, and Brown field operations.
- Greenfield operations get logged in the activity log; such operations include Policy assignment.
- Brownfield operations do not get logged in the activity log. Such operations include policy scan which is what happens when your resource changes to non-complaint on the Compliance blade. Currently there is no way to get Brownfield operations into Log Analytics or to create alerts with Brownfield operations because these Log Analytics and Alerts are dependent on logs from Activity Log.
However, if you want to get non-complaint resources in your portal, you can use Azure Resource Graph. Azure Resource Graph will help you query your resources which includes compliance states and display the results for you. You can go a step further and query the number of non-complaint policies, create a chart out of them and pin to your dashboard; this documentation explains how this is possible.
To perform a count query for a particular policy, for example the "Audit Resource Group for resource expiry date" to get the non-complaint policies kindly use this query below
policyresources | where properties['policyDefinitionName'] == "INSERT_VALUE_HERE" | where properties['complianceState'] == "NonCompliant" | summarize count() by tostring(properties.complianceState)