Hello @G-ONE ,
Thank you for posting here.
Here are the answer for your references.
**Q1:**So during Active Directory migration, servers(containing resources) have been migrated from source domain to target domain. Source Domain Local groups are applied in resource DACL. These source domain local groups have been migrated to target domain without Sidhistory and during migration group scope has been changed to "Global". These migrated global groups nested inside source domain local groups.
If target domain users are member of migrated global group and target users login to target domain joined workstation, then what Sids will be included in access token? Will target user's Access token include both - Sid of migrated target group as well as Sid of source domain local groups? Will target user be able to access resource?
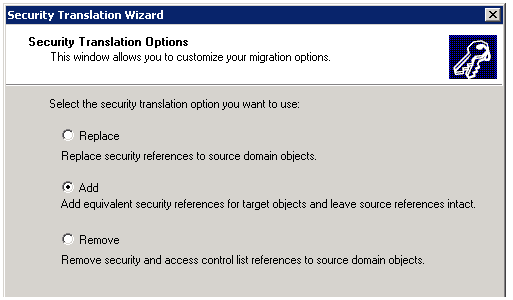
A1:**If you also perform Security Translation for this server, and select **"replace" Security translation options.
Access token will include target user SID and migrated group SID. Target user will be able to access resource.
If you also perform Security Translation for this server, and select "add" Security translation options.
Access token will include target user SID and migrated group SID. Target user will be able to access resource.
If you also perform Security Translation for this server, and select "remove" Security translation options.
Access token will include target user SID and migrated group SID. Target user will not be able to access resource.
Translating Security on Your Member Servers
https://video2.skills-academy.com/en-us/previous-versions/windows/it-pro/windows-server-2008-R2-and-2008/cc974389(v=ws.10)?redirectedfrom=MSDN
ADMT Series – 10. Security Translation Wizard – Local Profiles
https://blog.thesysadmins.co.uk/admt-series-10-security-translation-wizard-local-profiles.html
**Q2:**Another scenario: This time Servers (containing resources) are in source domain only. Source Domain Local groups are appended in resource DACL. These source domain local groups have been migrated to target domain without Sidhistory and during migration group scope has been changed to "Global". These migrated global groups nested inside source domain local groups.
If target domain users are member of migrated global group and target users login to target domain joined workstation, then what Sids will be included in access token? Will target user's Access token include both - Sid of migrated target group as well as Sid of source domain local groups? Will target user be able to access resource?
**A2:**Access token will include target user SID and migrated group SID. Target user will not be able to access resource.
**Q3:**In any of above mentioned scenarios, if target users will be able to access resource then how?
**A3:**See A1 and A2.
**Q4:**But here is the confusing part, then why and how trusted external users(trusted external domain) which are members of domain local security groups able to access resource which neither belongs to source domain nor target domain and they login to external domain joined workstation?
**A4:**Because there is trust, the users have the permissions to access the resource. It is related to cross-forest authentication, for more information about cross-forest authentication, we can refer to the part "Simple Cross-Realm Authentication and Examples" in the link below.
How the Kerberos Version 5 Authentication Protocol Works
https://video2.skills-academy.com/en-us/previous-versions/windows/it-pro/windows-server-2003/cc772815(v=ws.10)?redirectedfrom=MSDN
Hope information above is helpful. Ifanything is unclear, please feel free to let us know.
Best Regards,
Daisy Zhou