@FrankM-482
Thank for your time and patience throughout this issue!
Deny meaning, it denies to everyone except the ones we want to have access to it?
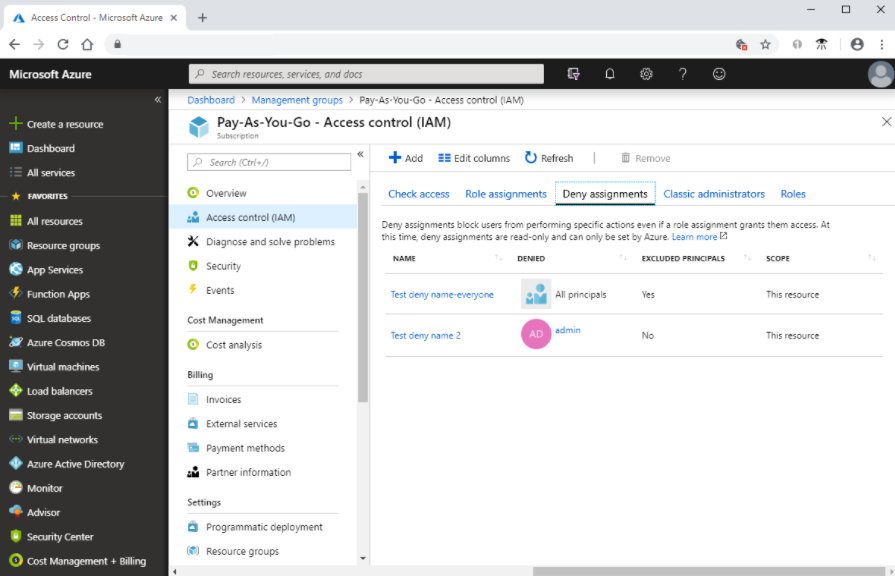
- Yes, you can create a Deny Assignment for all principals (all users, groups, service principals, and managed identities in an Azure AD directory). However, you can exclude some principals (i.e. certain users or groups) from this Deny assignment.
It seems like a good idea for something which has limited access to begin with but sounds difficult to implement when there a lot of users and groups which have access?
- When it comes to our RBAC best practices, to make role assignments more manageable, avoid assigning roles directly to users. Instead, assign roles to groups. Assigning roles to groups instead of users also helps minimize the number of role assignments.
It sounds like you're suggesting RBAC in that owners or administrators should know what type of access they are granting (or not granting) which could include not adding "guest" accounts to an IAM role?
- Yes. Users in an Owner/Admin role should follow our RBAC best practices documentation and only grant the access users need, rather than granting unneeded IAM roles to guest users.
If you have any other questions, please let me know.
Thank you for your time and patience throughout this issue.
----------
Please remember to "Accept Answer" if any answer/reply helped, so that others in the community facing similar issues can easily find the solution.