@PaulSchoorl-2684
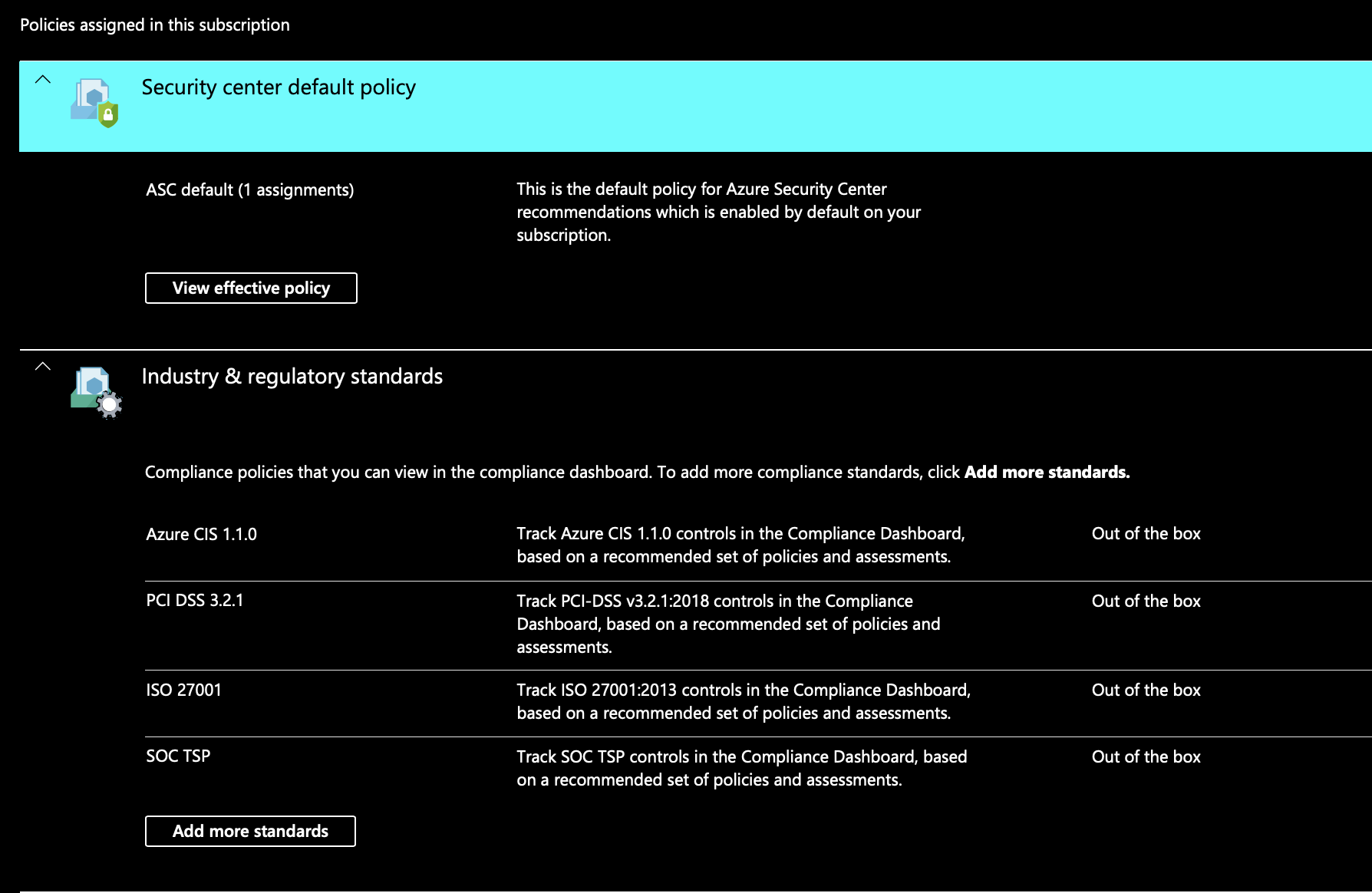
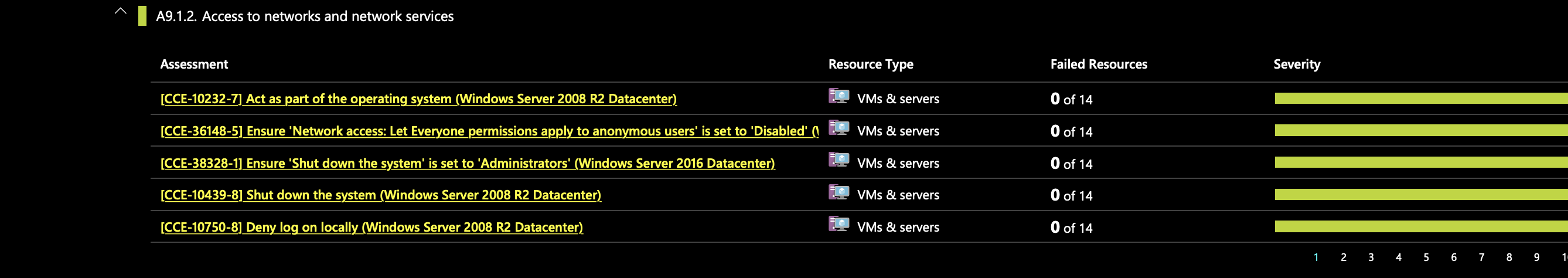
On the Industry and Standards section within Azure Security Center (ASC), those assessments look like they come from ISO 27001:2013. Azure Security Center also uses CCE (Common Configuration Enumeration) to assign unique identifiers for configuration rules. Based off my research and testing, you can manage and edit the security policies. However, you can't view the specific initiatives, or delete the definitions within the industry & regulatory standards. To customize policies to meet your organization's needs, you'd have to create a custom security policy. Additionally, I noticed that the default ASC supported regulatory standards: Azure CIS, PCI DSS 3.2, ISO 27001, and SOC TSP, aren't hyperlinks, so you can't view or delete those specific definitions inside the policy.
From the screenshot below, you can see that there's only a hyperlink on "Azure CIS 1.1.0 (New)", and not the default regulatory standards.
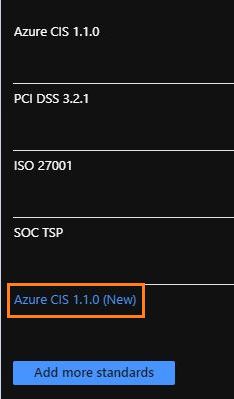
Within Azure CIS, you can see that I can't delete initiatives, I wasn't able to delete the definitions either.
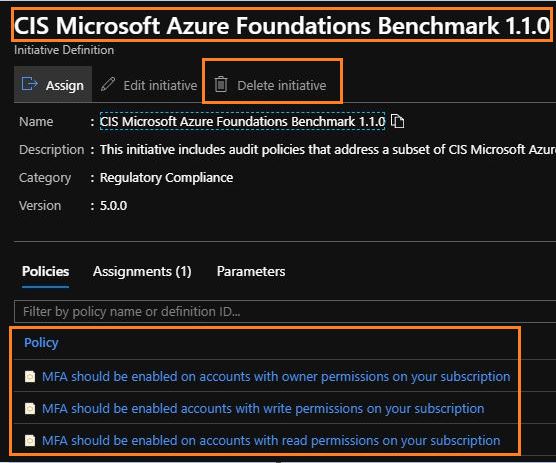
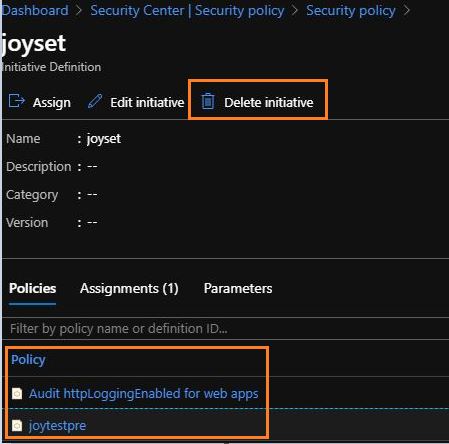
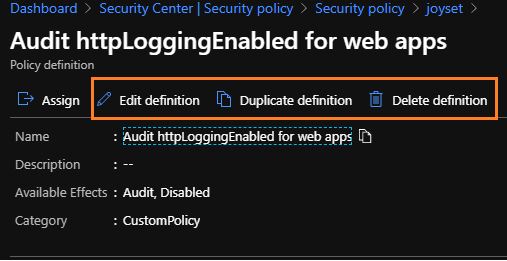
When I go into my custom policy, I'm able to edit or delete initiatives and definitions.
Please let me know if you have any other questions.
Thank you for your time!
Additional CCE Links:
Act as part of the operating system
Shut down the system
Deny log on locally
Network access: Let Everyone permissions apply to anonymous users