There is no interaction between ADFS and smartcard authentication for Windows.
You can set up certificate based authentication in ADFS but even that does not impact your abilities to do smartcard on Windows.
ADFS leaves traces of its installation in AD. Mainly containers which takes minimum space. So doesn't even need to be cleaned up. They are under <domain name>/Program Data/Microsoft/ADFS. You will need to enable the Advanced Features view option in the Users and Computers MMC to see them (and you will need to be a member of Domain admins or the built-in Administrators to see and delete them).
Unless you mean ADCS? If so tell us :)
Smartcard authentication requires the domain to have the certificate of the smartcard certificate issuing CA in the NTAuth store (which seems to be the case for you) and the root certificate of the CA that issued that certificate in the RootCA store (which also seems to be the case for you). You can verify that the certificates are in fact really there by using the PKIVIEW.MSC tool. This tool requires you to use the Active Directory Certificate Services administrative tools (with the RSAT on Windows 10 or with the Server Manager by adding the feature).
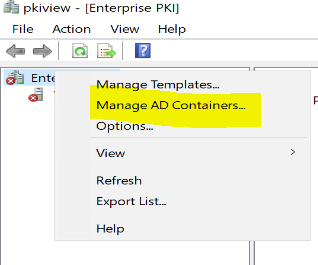
This tool works to see the AD stores graphically even if you use a third party CA. You can see all the data in other tools such as LDP.EXE or ADSIEDIT.MSC or even DSSITE.MSC but then most of the data is in binary format.
Smartcard authentication requires the user to have a certificate with the Smart Card Logon EKU.
Smartcard authentication requires the device to have a smartcard reader :)
