@kumar kaushal , In Azure, NSG's are proactive in learning to and fro flows. You may not create two security rules with the same priority and direction. A flow record is created for existing connections.
Communication is allowed or denied based on the connection state of the flow record. The flow record allows a network security group to be stateful.
If you specify an outbound security rule to any address over port 80, for example, it's not necessary to specify an inbound security rule for the response to the outbound traffic. You only need to specify an inbound security rule if communication is initiated externally. The opposite is also true. If inbound traffic is allowed over a port, it's not necessary to specify an outbound security rule to respond to traffic over the port.
Do provide your NSG rule SS for providing better insights. Also, there should not be any issue with traffic flows if you have an NSG like specified below,
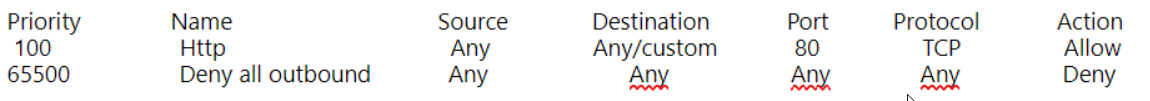
Note: Make sure you have this rule unaltered in the outbound rule section,
65001 AllowInternetOutBound Any Any Any Internet Allow
----------
Please do not forget to "Accept the answer" wherever the information provided helps you to help others in the community.
