Hi @Swebhi ,
I think you need to follow the Hub-Spoke design for deploying the Azure Firewall, you can have a look at the design over here. I will split the VNET and have it specific for FW but depends on your requirements and options you have.
There is Azure FW Standard and Azure FW Premium both has different features and pricing so have at that.azure-firewall
Or you can have it in Hub VNET and let the traffic pass through it for internal network
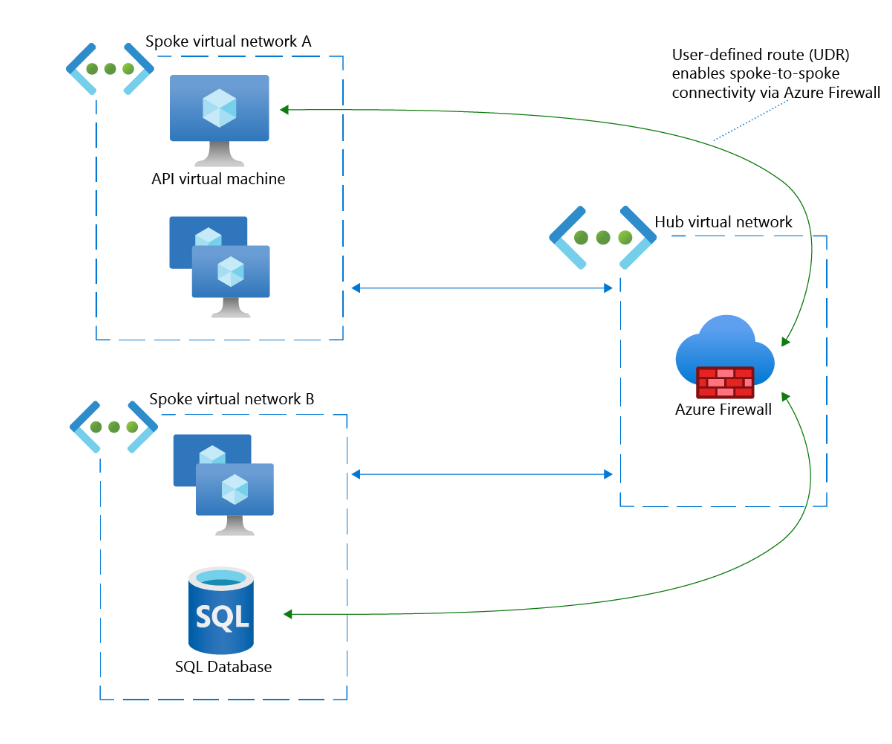
Azure Firewall is best deployed using a hub and spoke network topology with the following characteristics:
A virtual network that acts as the central connectivity point. This network is the hub virtual network.
One or more virtual networks that are peered to the hub. These peers are the spoke virtual networks and are used to provision workload servers.
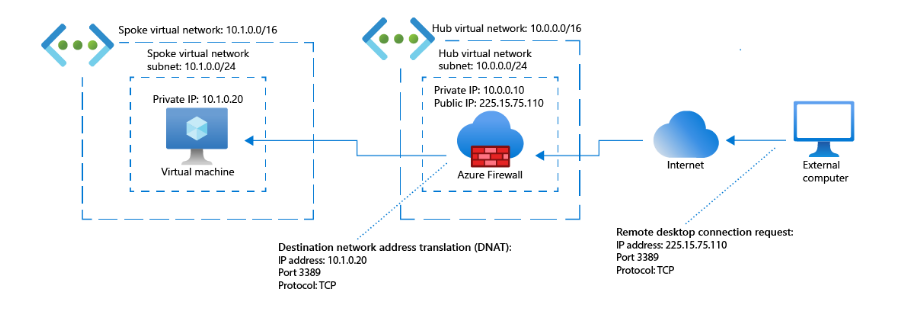
You deploy the firewall instance in a subnet of the hub virtual network and then configure all inbound and outbound traffic to go through the firewall.
Use the following general steps to set up an instance of Azure Firewall:
Create a hub virtual network that includes a subnet for the firewall deployment.
Create the spoke virtual networks and their subnets and servers.
Peer the hub and spoke networks.
Deploy the firewall to the hub's subnet.
For outbound traffic, create a default route that sends traffic from all subnets to the firewall's private IP address.
Configure the firewall with rules to filter inbound and outbound traffic.
==
Please "Accept the answer" if the information helped you. This will help us and others in the community as well.

