Update on UAC
Hi, Jon DeVaan here to talk to you about the recent UAC feedback we’ve been receiving.
Most of our work finishing Windows 7 is focused on responding to feedback. The UAC feedback is interesting on a few dimensions of engineering decision making process. I thought that exploring those dimensions would make for an interesting e7 blog entry. This is our third discussion about UAC and for those interested in the evolution of the feature in Windows it is worth seeing the two previous posts (post #1 and post #2) and also reading the comments from many of you.
We are flattered by the response to the Windows 7 beta so far and working hard at further refining the product based on feedback and telemetry as we work towards the Release Candidate. For all of us working on Windows it is humbling to know that our work affects so many people around the world. The recent feedback is showing us just how much passion people have for Windows! Again we are humbled and excited to be a part of an amazing community of people working to bring the value of computing to a billion people around the world. Thank you very much for all of the thoughts and comments you have contributed so far.
UAC is one of those features that has a broad spectrum of viewpoints with advocates staking out both “ends” of the spectrum as well as all points in between, and often doing so rather stridently. In this case we might represent the ends of the spectrum as “security” on one end and “usability” on the other. Of course, this is not in reality a bi-polar issue. There is a spectrum of perfectly viable design points in between. Security experts around the world have lived with this basic tension forever, and there have certainly been systems designed to be so secure that they are secure from the people who are supposed to benefit from them. A personal example I have, is that my bank recently changed the security regimen on its online banking site. It is so convoluted I am switching banks. Seriously!
Clarifying Misperceptions
As people have commented on our current UAC design (and people have commented on those comments) it is clear that there is conflation of a few things, and a set of misperceptions that need to be cleared up before we talk about the engineering decisions made on UAC. These engineering decisions have been made while we carry forth our secure development lifecycle principles pioneered in Windows XP SP2, and most importantly the principle of “secure by default” as part of SD3+C. Windows 7 upholds those principles and does so with a renewed focus on making sure everyone feels they are in control of their PC experience as we have talked about in many posts.
The first issue to untangle is about the difference between malware making it onto a PC and being run, versus what it can do once it is running. There has been no report of a way for malware to make it onto a PC without consent. All of the feedback so far concerns the behavior of UAC once malware has found its way onto the PC and is running. Microsoft’s position that the reports about UAC do not constitute a vulnerability is because the reports have not shown a way for malware to get onto the machine in the first place without express consent. Some people have taken the, “it’s not a vulnerability” position to mean we aren’t taking the other parts of the issue seriously. Please know we take all of the feedback we receive seriously.
The word “vulnerability” has a very specific meaning in the security area. Microsoft has one of the leading security agencies in the world in the Microsoft Security Response Center (secure@microsoft.com) which monitors the greater ecosystem for security threats and manages the response to any threat or vulnerability related to Microsoft products. By any definition that is generally accepted across the world wide security community, the recent feedback does not represent a vulnerability since it does not allow the malicious software to reach the computer in the first place.
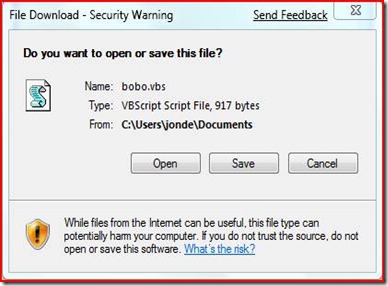
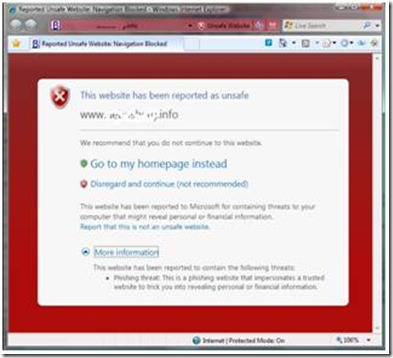
It is worth pointing out the defenses that exist in Windows Vista that keep malware from getting on the PC in the first place. In using Internet Explorer (other browsers have similar security steps as well) when attempting to browse to a .vbs file or .exe file, for example, the person will see the prompts below:
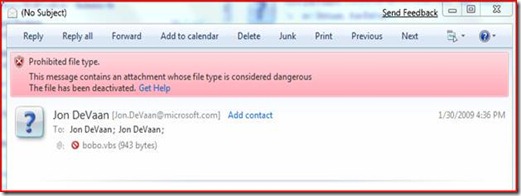
Internet Explorer 8 has also introduced many new features to thwart malware distribution (see https://blogs.msdn.com/ie/archive/2008/08/29/trustworthy-browsing-with-ie8-summary.aspx ). One of my favorites is the SmartScreen® Filter which helps people understand when they are about to visit a malicious site. There are other features visible and hidden that make getting malware onto a PC much more difficult.
A SmartScreen® display from IE 8
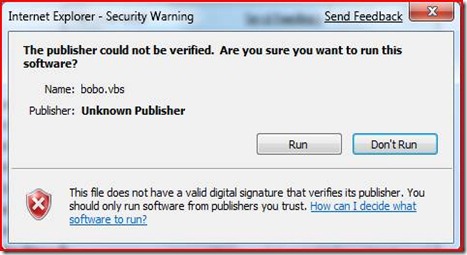
Additionally, if one attempts to open an attachment in a modern email program (such as Windows Live Mail) the malware file is blocked:
Much of the recent feedback has failed to take into account the ways that Windows 7 is better than Windows Vista at preventing malware from reaching the PC in the first place. In Windows 7 we have continued to focus on improving the ability to stop malware before it is installed or running on a PC.
The second issue to untangle is about the difference in behavior between different UAC settings. In Windows 7, we have four settings for the UAC feature: “Never Notify,” “Notify me only when programs try to make changes to my computer (without desktop dimming),” “Notify me only when programs try to make changes to my computer (with desktop dimming),” and “Always Notify.” In Windows Vista there were only two choices, the equivalent of “Never Notify” and “Always Notify.” The Vista UI made it difficult for people to choose “Never Notify” and thus choosing between extremes in the implementation. Windows 7 offers you more choice and control over this feature, which is particularly interesting to many of you based on the feedback we have received.
The recent feedback on UAC is about the behavior of the “Notify me only when programs try to make changes to my computer” settings. The feedback has been clear it is not related to UAC set to “Always Notify.” So if anyone says something like, “UAC is broken,” it is easy to see they are mischaracterizing the feedback.
The Purpose of UAC
We are listening to the feedback on how “Notify me only when…” works in Windows 7. It is important to bring in some additional context when explaining our design choice. We choose our default settings to serve a broad range of customers, based on the feedback we have received about improving UAC as a whole. We have learned from our customers participating in the Customer Experience Improvement Program, Windows Feedback Panel, user surveys, user in field testing, and in house usability testing that the benefit of the information provided by the UAC consent dialog decreases substantially as the number of notifications increases. So for the general population, we know we have to present only key information to avoid the reflex to “answer yes”.
One important thing to know is that UAC is not a security boundary. UAC helps people be more secure, but it is not a cure all. UAC helps most by being the prompt before software is installed. This part of UAC is in full force when the “Notify me only when…” setting is used. UAC also prompts for other system wide changes that require administrator privileges which, considered in the abstract, would seem to be an effective counter-measure to malware after it is running, but the practical experience is that its effect is limited. For example, clever malware will avoid operations that require elevation. There are other human behavior factors which were discussed in our earlier blog posts (post #1 and post #2).
UAC also helps software developers improve their programs to run without requiring administrator privileges. The most effective way to secure a system against malware is to run with standard user privileges. As more software works well without administrator privileges, more people will run as standard user. We expect that anyone responsible for a set of Windows 7 machines (such as IT Administrators or the family helpdesk worker (like me!)) will administer them to use standard user accounts. The recent feedback has noted explicitly that running as standard user works well. Administrators also have Group Policy at their disposal to enforce the UAC setting to “Always Notify” if they choose to manage their machines with administrator accounts instead of standard user accounts.
Recapping the discussion so far, we know that the recent feedback does not represent a security vulnerability because malicious software would already need to be running on the system. We know that Windows 7 and IE8 together provide improved protection for users to prevent malware from making it onto their machines. We know that the feedback does not apply to the “Always Notify” setting of UAC; and we know that UAC is not 100% effective at stopping malware once it is running. One might ask, why does the “Notify me only when…” setting exist, and why is it the default?
Customer-Driven Engineering
The creation of the “Notify me only when…” setting and our choice of it as the default is a design choice along the spectrum inherent in security design as mentioned above. Before we started Windows 7 we certainly had a lot of feedback about how the Vista UAC feature displayed too many prompts. The new UAC setting is designed to be responsive to this feedback. A lot of the recent feedback has been of the form of, “I’ll set it to ‘Always Notify,’ but ‘regular people’ also need to be more secure.” I am sure security conscious people feel that way, and I am glad that Windows 7 has the setting that works great for their needs. But what do these so called “regular people” want? How to choose the default, while honoring our secure design principles, for these people is a very interesting question.
In making our choice for the default setting for the Windows 7 beta we monitored the behavior of two groups of regular people running the M3 build. Half were set to “Notify me only when…” and half to “Always Notify.” We analyzed the results and attitudes of these people to inform our choice. This study, along with our data from the Customer Experience Improvement Program, Windows Feedback Panel, user surveys, and in house usability testing, informed our choice for the beta, and informed the way we want to use telemetry from the beta to validate our final choice for the setting.
A key metric that came out of the study was the threshold of two prompts during a session. (A session is the time from power up to power down, or a day, whichever is shorter.) If people see more than two prompts in a session they feel that the prompts are irritating and interfering with their use of the computer. In comparing the two groups we found that the group with the “Always Notify” setting was nearly four times as likely to have sessions with more than two prompts (a 1 in 6.7 chance vs a 1 in 24 chance). We gathered the statistic for how many people in the sample had malware make it onto their machine (as measured by defender cleaning) and found there was no meaningful difference in malware infestation rates between the two groups. We will continue to collect data during the beta to see if these results hold true in a much broader study.
We are very happy with the positive feedback we have received about UAC from beta testers and individual users overall. This helps us validate our “regular people” focus in terms of the trade-offs we continue to consider in this design choice. We will continue to monitor the feedback and our telemetry data to continue to improve our design choices on UAC.
So as you can see there is a lot of depth to the discussion of UAC and the improvements made in Windows 7 in UAC itself and in improving ways to prevent malware from ever reaching a PC. We are working hard to be responsive to the feedback we received from Vista to provide the right usability and security for people of all types. We believe we’ve made good progress and are listening carefully to the feedback on our UAC changes. Again please accept our most sincere thanks for the passion and feedback on Windows 7. While we cannot implement features the way each and every one of you might wish, we are listening and making a sincere effort to properly weigh all points of view. Our goal is to create a useful, useable, and secure Windows for all types of people.
Jon
Comments
Anonymous
February 04, 2009
The comment has been removedAnonymous
February 04, 2009
The comment has been removedAnonymous
February 04, 2009
The comment has been removedAnonymous
February 04, 2009
I think there it's still missing the point. It's a good balance to have the defaults as they are in the Windows 7 beta. The issue is making sure they stay that way. Having a prompt just for changing the UAC settings would be extremely unlikely to change the 2 per-session guideline (after all, you aren't going to be changing it often) but would prevent malware that has made it through the existing defences from changing the setting even lower. Just because it isn't a security vulnerabilty doesn't mean that it's behaviour makes sense.Anonymous
February 04, 2009
While UAC may not be a security boundary, when the Operating System's default state allows any application to trivally have the System elevate arbitrary code, you no longer have a useful tool at all. And the sources of malicious code are far more than that downloaded via Internet Explorer or an attachment-minding email client. The long and the short of it is the token needed to adjust the UAC setting should be something above that granted by the autoElevate system.Anonymous
February 05, 2009
Jon, you're missing the point. The people only want to see an UAC notification when the UAC level is changed. That's all. You don't have to change anything else.Anonymous
February 05, 2009
I'm not sure you only have to protect the UAC level. Does the default setting allow an application to do the following without any notification? ... only if Im an administrator or if Im a user?: Replace a windows .dll Uninstall a driver Change services Add executable to startup ... etc Assuming an app could do all of this silently, what good is UAC for at this point anyway. Why not just remove it. -dAnonymous
February 05, 2009
While I understand that you do not consider UAC the ultimate barrier against malware, even with all the new security barriers in mail, IM and IE8 you saw that it did not prevent for malware to be installed. So, a new barrier should be running to prevent the installed malware to harm the computer. Naturally, this barrier can be the UAC (although I'm pretty sure a lot of malware can run in user mode if its just collecting data..)Anonymous
February 05, 2009
with all those REQUEST , become 40 SKU of Windows 7 :DAnonymous
February 05, 2009
I think the point that it shouldn't be so easy for an application to elevate itself hasn't been answered in the post. The comments so far explain the situation very well though, I don't see why microsoft don't want to remove or change the way auto-elevation works.Anonymous
February 05, 2009
Look at it this way - let's say I let my son bring a friend over, even one who I thought was trustworthy. I dont need to be notified if he takes a drink from my fridge or sits on my chair. But I'd REALLY like to be notified if he's trying to remove the locks to my bedroom door. The changing of the UAC setting itself must be an exception. It is a fundamentally different setting than any other setting. I simply dont understand how this is not painfully obvious. If not for the reality of this situation, then for the perception. If you guys are correct, the only people that should see this are people already infected with malware, so a second reminder that something really fishy is going on is not going to hurt.Anonymous
February 05, 2009
Wow. Wrong answer. The Microsoft response to this issue is really shaking my faith the quality of Windows 7. Vista was full of the sort of obtuse thinking. Every single person outside of Microsoft knows the fix for this, its mentioned multiple times in the comment in this thread. Put on your "common sense" hat and just fix the issue, guys. It's not that difficult.Anonymous
February 05, 2009
I think part of the issue here is the fact that there is an assumption that any untoward goings on will only ever be caused by malware or spyware. As far as Im concerned, no application trusted or otherwise, should be able to alter the core UAC settings without express permission from the user (via a UAC prompt). As it currently is in the beta, any application running on the system can very easily and silently disable UAC completely, thereby giving itself and any other app that wants it, full access to the system. That alone completely nullifies the point of having UAC or any other security boundary in the first place, if it can be so easily tampered with by any running process. I do agree with Microsoft's assertion that UAC was not specifically designed as a fool proof security barrier, but it is however an important part of Windows' security model and should be treated as such. As it currently is in the beta, it can be so easily disabled it may as well not be there at all. As others have pointed out, the default setting is fine (And works well) but there certainly needs to be some kind of prompt when attempting to change UAC's core settings.Anonymous
February 05, 2009
Sometimes, inconsistency with your own ideals is a good thing. Make an exception, if only to put people's fears to rest.Anonymous
February 05, 2009
I see your point that the malware should never get onto the computer in the first place, but imagine if I downloaded a piece of software that unknown to me had malware piggybacking on it. I would click through the UAC promts thinking I was installing a legit program, while in the background this program is also being installed. Rafael Rivera's list of EXE's that can be evelevated without promting UAC is sligtly scary! All you would have to is prompt when the UAC level changes or is changed. Just another UI idea for UAC, a checkbox with "Don't prompt UAC for This Program Again." would be HUGE! The list of allowed programs could be managed in the control panel. Anyway, thanks for all your work on UAC!Anonymous
February 05, 2009
Jon, let me quote poster above, just in case you missed it: " Jon, you're missing the point. The people only want to see an UAC notification when the UAC level is changed. That's all. You don't have to change anything else. " Please stop giving @! excuses. It is not working as expected. Surely if I run vbs script I don't expect it to be able to completely turn off UAC. Let me know if it tries to change my UAC settings. That is all. Thanks.Anonymous
February 05, 2009
Don't deal with treat UAC settings like Windows settings, this would cause UAC prompt when people change UAC settings, would be a perfect solution in my opinion. In this situation there are no reductions in security and usability.Anonymous
February 05, 2009
Think of it like the security/ID badges you use at work. If you are authorized to enter a certain area, this is reflected by your badge and you walk right in. If you are not, then you must show some documentation granting permission. This would be a UAC prompt. If the change is to be made permanent and you are given full access you would still expect to the change to be validated before being granted access. This is a UAC prompt for UAC changes. Why should it be easier to get permanent access to a controlled resource than to get temporary access? Sure, no one in the company SHOULD be asking for access if they are not supposed to have it, but that doesn't mean they won't. Why should it be easier to turn off UAC than to act maliciously with UAC? Sure, no malware SHOULD be running on the PC, but that doesn't mean it won't. 1 additional prompt that very few people will ever see and it greatly increases the faith people have in this whole system. If I know that changes needing elevation will be prompted and I don't see any prompts, I feel fine. If I know that at any time, UAC prompts could be disabled without prompting, then I would immediately turn it up to full and live with the extra hassle. I rarely ever leave comments anywhere. In fact I had to register just to leave this comment, but I feel strongly enough about this issue that it definitely warrants attention.Anonymous
February 05, 2009
The comment has been removedAnonymous
February 05, 2009
I really like UAC. No, wrong, I LOVE UAC. And John, you are right in all points and it everything you say is correct. However most people are worried about the issue mentioned here: http://www.istartedsomething.com/20090130/uac-security-flaw-windows-7-beta-proof/ So I'd like to provide a little different view and ask: Why do you force people to enter the old password when changing it? In fact they already had to enter the password when logging on to their PC so why bother with it again? Answer: Because it's more secure. Why not take the same route with UAC and always ask about elevation when the elevation settings are changed? Even if it wouldn't be more secure (according to your studies) people would at least FEEL more secure - and that is most important for technical folks. Kind regards, OohAnonymous
February 05, 2009
> "The people only want to see an UAC > notification when the UAC level is > changed. That's all." Remember that today in Windows, just about any setup.exe program you run will automatically prompt you to elevate since it usually needs admin rights. At that point you are pwned anyway. An evil setup program has no need to disable UAC. If it decides to do so, it would most likely change the registry setting directly rather than go to the trouble of pushing keystrokes into the UI the way Long Zheng's "exploit" did. So can anyone explain a scenario where this one extra annoy-o-gram ("You are attempting to change the UAC setting via the Windows dialog, please confirm") is going to have any real effect?Anonymous
February 05, 2009
The comment has been removedAnonymous
February 05, 2009
The comment has been removedAnonymous
February 05, 2009
The comment has been removedAnonymous
February 05, 2009
One final thought- Microsoft should fix this "problem" even if not considered a vulnerability, if for no other reason than to get Win 7 off on the right foot. After Vista they could use some good press and rumors of a security problem before launch won't help.Anonymous
February 05, 2009
@xiphi: UAC can be configured on Windows 7 to behave exactly as it does on Vista. You only have that problem with the default configuration. @Ooh: I agree with you. Although I can see the point MS is making, now it's a matter of perceived security (and bad press).Anonymous
February 05, 2009
The comment has been removedAnonymous
February 05, 2009
My conspiracy theory is that Microsoft disabled UAC by default in Windows 7 to raise this very discussion which even got its way into printed press. Their goal is to make us ask to have UAC in “Always Notify” mode in RTM. And I do ask that because people I know don’t have any issues with Vista UAC because they only use Internet Explorer and Microsoft Word. When I first heard about UAC changes what I hoped for was more granular control over changes. I mean why you need UAC to change DPI? What kind of malware might want to change DPI? And that was changed in Windows 7. There is no UAC prompt to change DPI in Windows 7. Here we have another thing which is to allow specially signed executables to change critical settings without UAC prompt. Here is interesting thing. With UAC in “notify only when programs try…” mode I am still presented with UAC prompt when I try to run regedit.exe (WHY??). But if I go and disable UAC at all – which is allowed without any prompt I immediately can go and run regedit.exe without any UAC Prompt. If MS does not allow running regedit.exe in “broken-UAC” mode why does it allow switching UAC mode off? This all seems very inconsistent. I have switched to “always notify” mode.Anonymous
February 05, 2009
The comment has been removedAnonymous
February 05, 2009
The comment has been removedAnonymous
February 05, 2009
Jon, Thanks for sharing your thoughts. I understand your points. Now, I want add my voice to the call for one very simple change: Treat the UAC prompting level as a special case, such that ANY change to it, whether from the user or a program, generates a UAC prompt, regardless of the type of account the user has, and regardless of the current prompting level. That is all we are asking. No other changes. Leave the default level as it is, and keep UAC as it is. We're just talking about the very specific case of CHANGES to the UAC prompting level. It will NOT be a big nuisance - most people only ever change the UAC level once (if at all). Despite your assurances, I REALLY WANT TO KNOW if anything tries to alter the UAC prompting level. The fact that nobody has yet demonstrated how the putative malware can get into your machine is NO argument. Somebody WILL get past those other boundaries eventually. Even if you aren't convinced by my argument, then the PR argument must be a no-brainer for Microsoft. PLEASE, Jon, it's just a small change that will gain a LOT of user confidence and a LOT of good PR. ThackAnonymous
February 05, 2009
I definitly agree with the idea to add an option when installing windows to create both a local admin account as well as a standard-user account. That would be a huge help in encouraging the use of standard-user accounts. I also agree that even if you guys don't think it's a big issue, there are lots of people in the real world that do. You keep saying you listen to your customers, listen to us and at least add a prompt when changing the UAC notification level.Anonymous
February 05, 2009
I don't get this mind-boggling, the-customer-is-stupid response! If 7 can keep malware off of the computer, what is the point of UAC at all that I, as an individual customer, care about? Look, just fix this little issue. Laugh at me behind my back, send little sarcastic emails amongst yourselves, I don't care, just don't force my to set UAC to "Always Notify", please. I'll sleep better at night.Anonymous
February 05, 2009
The comment has been removedAnonymous
February 05, 2009
Am I missing something. Could Microsoft not setup mechanism to allow only an authorized subsystem to change the UAC settings or disable it altogther. ie digitially signedAnonymous
February 05, 2009
You have 95% of the people out there think you got it wrong, even if they are the ones that got it wrong. The problem is that they are the one's that buy and recommend your product. So do you give them a false sense of increased security by implementing the change (not unlike security by obscurity) and making them happy, or do you just fortify the real security boundaries? Personally, I think you make people happy and sell product. Though acknowledge that you will suddenly have lots of similar items in the same class of "I installed something and it is doing something I didn't think it would do". The general public understands and appreciates security by obscurity (they still hide things under the mattress, or someplace hidden in their house), even though the security industry thinks it is bad since it brings a false sense of security that they do not have. But people relate to it anyhow. Doesn't sound like an engineering decision. Sounds like a business one.Anonymous
February 05, 2009
The comment has been removedAnonymous
February 05, 2009
Jon, this is unbelievable. Such a long blog entry and you never come to the point. How long do you want to hide behind telemetry data? This is not a way to communicate with smart people. You are either dumb (don't think so) or you make yourself look like dumb because you have actually seen through this. First the question of how malware comes to run on the computer is completely irrelevant for this, because UAC prompts are about programs which already run on the computer. One question really raised here is if the UAC prompt is special for UAC or not. Maybe you think it is not special and have a good reason for that. But I can't imagine that a smart guy did not see this question asked here. So I think what you do not tell us here is that you fear if you give in in this case and put an UAC prompt before UAC changes, people will come up with further cases where programs bypass UAC by simulating user input rendering the whole concept of the new default setting useless. But then maybe it is useless. Obviously this would be hard for you to swallow at this point. But you have more to lose by not having an honest discussion.Anonymous
February 05, 2009
I think a clarification on whether UAC can be changed programmatically and whether there will always be a UAC prompt if this happens would help here... but the figures on usage and malware incidence from the M3 are very interesting. Do you consider the M3 user base representative of the general user base or might there be a skew towards more 'careful' users? I'm assuming you'll look at the same figures from beta users and evaluate that...Anonymous
February 05, 2009
As many said before me: Changing UAC Prompting Level should trigger an UAC prompt!Anonymous
February 05, 2009
Shouldn't chaning the UAC Level be the ONE command above all commands that produces the UAC Prompt? I wouldn't not give someone the keys to my house, but allow them to easily change all the locks on my doors... Just doesn't make any sense. What am I missing?Anonymous
February 05, 2009
The comment has been removedAnonymous
February 05, 2009
The comment has been removedAnonymous
February 05, 2009
The comment has been removedAnonymous
February 05, 2009
The comment has been removedAnonymous
February 05, 2009
I feel that Windows or Setup does not encourage users enough to run as normal user. Most users that are mostly the only users of their computer create only 1 user account and that becomes the account with admin rights. Setup should be changed in a way that it becomes normal for any computer user that a normal user account is created that will be used normally, and that the admin account is only used for very specific scenario's.Anonymous
February 05, 2009
The comment has been removedAnonymous
February 05, 2009
I think the big unword in this article is "Customer-Driven Engineering". Customers will always ask for more gummi bears. But if they get problems with their stomach, then it is of course the fault of the engineer.Anonymous
February 05, 2009
The comment has been removedAnonymous
February 05, 2009
I would suggest the Microsoft security group work with the Comodo team on how to properly display a popup, how to display the information (have a Basic and an Advanced option), AND how to properly implement a firewall. The XP, Vista and W7 firewalls are so useless that any script kiddie with more than 10 minutes can be into the OS (direct broadband connection, no NAT firewall, no software firewall aside of default Windows Firewall). UAC is only useful for the clueless customer that wants that warm fuzzy feeling of "thinking" that they are safe with UAC on.Anonymous
February 05, 2009
Previously, I mentioned that Defender's detection rates aren't too great. As an illustration, I pulled 2236 malware samples out of my archives, and scanned them with Defender, as well as with Kaspersky's online scanner. Here are screenshots showing the results (namely, Defender detects 95 of the 2236 samples, while Kaspersky detects 2216 of them). http://i240.photobucket.com/albums/ff237/mechBgon/Defender.png http://i240.photobucket.com/albums/ff237/mechBgon/Kaspersky.png Keep in mind that these samples are more than a year old. I hope the Win7 team is also using other software, such as OneCare or another full antivirus program, to generate metrics on infection rates.Anonymous
February 05, 2009
I think that there is NO way to make that "broken-UAC" to work at all. Instead I would like to see sime kind of "don't warn me for the next 30 minutes" option in the UAC screen. Also I would like to have special UAC mode in which it is allowed to do different not very harmful things like list running processes from All Users in Task Manager, launch chkdsk.exe or defrag, even connect or disconnect from network. But replacing system files in Windows Explorer, updating device driver, change security permissions - all these should be UAC protected.Anonymous
February 05, 2009
Great explanation on UAC and how MS puts so much faith in the very narrow & limited user groups and surveys, instead of relying on 'real' users in the field as represented mainly by their many beta testers who DO represent and deal with the 'ordinary users' every day. This blog post, while eloquently presented, says one thing mainly: 'that MS, again, can't see the forest for the trees'. :)Anonymous
February 05, 2009
@Mikael3 You are right. The new UAC level is definitely flawed and they have a deeper design problem here that is not fixed by just adding a single prompt. If they were to add a prompt for UAC changes then someone would come along and do a quick demo on "How to turn of the W7 firewall without UAC prompting for elevation". They really have to reconsider the current implementation of the new UAC level and I think (as mentioned earlier) a more extensive use of integrity levels could possibly do the job here. It would be interesting to see Jon commenting on such ideas.Anonymous
February 05, 2009
I'd accept that this is quite a valid argument. UAC can only protect you so much, but the onus is on your part to not click yes to run anything, but that also leads to one issue, where people can further circumvent this and make things seem more legit, and that is through an MSI installer, just imagine applications bundled with the reg key. I mean elevating for an MSI installer is pretty common, and if the malware vendor or what not, is intending to try to give away free software and also in turn getting the user to elevate the install so that they can install the reg key, then it's really not the users fault to unknowingly allowing elevation, as the installer could be well packaged really nicely and the app could very well be an excellent app, giving good incentives to the user.Anonymous
February 05, 2009
The comment has been removedAnonymous
February 05, 2009
Is no one else surprised that malware can change UAC settings? There should be absolutely no method for applications to change UAC settings in the first place. And users should always be prompted for decreasing UAC settings, the above example of someone letting their child use their PC is a good reason why this should be the case. Sure, malware has to be prompted to allow these things to run, but, at least in Vista, when the malware is removed UAC is still there at the end of the day. On 7, once it's disabled it will probably remain that way for a while as users aren't likely to re-enable a feature that "nags" or "second-guesses" them. By-the-by, this post sure has gotten a lot of responses quickly. The nerds are angry! :-)Anonymous
February 05, 2009
The comment has been removedAnonymous
February 05, 2009
@bluvg As I stated before, it is not sufficient to add a prompt for the UAC level settings dialog. This dialog is just one example of using "certified for auto-elevation" applications/dialogs to render the new UAC level useless (although it is an extreme example). A malware could still turn off the firewall, make changes to system folders and mess around with other sensitive system settings at standard UAC level. An additional prompt for the UAC settings dialog just prevents the malware from turning off UAC completely (at least if malware cannot use the sending of keystrokes to change registry keys).Anonymous
February 05, 2009
The comment has been removedAnonymous
February 05, 2009
I want to thank everyone for their energy and comments. It is really exciting to be part of such a passionate community! Yes, even when we are having a spirited debate. Steven and I just posted a follow up where we describe how we want to move forward based on the feedback today. I encourage everyone to read that. I am sure many people will be very happy! As I described in my post, we will continue to listen to the feedback and improve our design of the UAC feature. @Thack: Thank you very much for your post! I was hoping that I was going to be able to reach people who could understand our reasoning and then provide clear feedback in that context. @mechBgon: Thank you for this feedback on better ways to measure malware infestation. It is very constructive. We only had defender in the sample study. We will be sure to use better sources for the beta study. @artfudd: Please be fair. I am glad to share my point of view transparently and accept the full criticism from the community (some posts get more criticism than others :-)). I won’t claim our data gathering is perfect, but it is valuable to understand what is really going on vs. what we think is going on in the real world. This does not diminish our desire to hear from and be responsive to our beta testers. Some of the comments are attributing sentiments to me in the post that I did not intend. I sincerely apologize for any bugs in the post. I hope that taking the time to explain our thinking is not automatically assumed to be closed minded. I will work on my ability to put myself more in your shoes when I communicate in the future so that my communication is clearer. I remain sincere in my statement that we are listening carefully to the all of feedback and that we will use it to improve the UAC feature. Thank you again for engaging with us and helping us make Windows 7 great! JonAnonymous
February 05, 2009
The comment has been removedAnonymous
February 05, 2009
The comment has been removedAnonymous
February 05, 2009
The comment has been removedAnonymous
February 05, 2009
I agree with the comments above! Under no circumstances should any program be able to make silent changes to UAC. Every single UAC level change should show the secure desktop and require user input. NO OTHER CHANGES TO W7 UAC ARE NEEDED! I can't believe that MS doesn't get this...boggles my mind. If MS leaves W7 the way it is, UAC is completely worthless and should be removed from the OS.Anonymous
February 05, 2009
The comment has been removedAnonymous
February 07, 2009
@MaryPCB I hope you are right, but the real trouble is that as I am a consultant I am honour bound to make them aware of all the different versions. If I know that there are different versions I have to explain them and give my reasons for why I would avoid version A over Version B. It would just be a lot simpler if they kept the complexity down. I would rather have the two versions and use the option to add bits like they are doing with the unbundling of things like Windows Mail, so that the user can add bits as they like or need. We are into a tough period economically and keeping the prices down and complexity down I feel will be the best policy. Sorry again, I know, off topic! SivAnonymous
February 07, 2009
OK, I really think EVERYONE has missed the point that this doesn't have to be MALWARE! I can download any legitimate program, and it could internally turn UAC off without me knowing. This could simply be a matter of the programmer was too lazy to write it to be 'compatible' with UAC, but the fact remains, this isn't malware. So, the design decision they have made is bad, since it allows good intentioned people to do bad things, and make my system vulnerable. Yes, there's a lot of other things that same programmer could do to make my system vulnerable, but this is one that can easily be fixed. How hard could it be to add another 'if' statement to the code? cdAnonymous
February 11, 2009
The comment has been removedAnonymous
February 27, 2009
I found out that while it is necessary to accept UAC prompt to turn OFF Windows Defender with Windows 7 Beta, turning ON defender in standard account do not trigger the UAC prompt. Yes, I have set the UAC prompt at its highest level. I think they made this change “by design”, but it doesn’t conform to consistent experience. If turning OFF is an administrative task, so is turning ON. This could create a lot of problems to administrators especially using third party anti-spyware solution & turns OFF windows defender. The standard account users may turn on windows defender without permission causing the computer to slow down.Anonymous
March 13, 2009
And we don't want our computer to slow down!Anonymous
June 12, 2009
They really have to reconsider the current implementation of the new UAC level and I think (as mentioned earlier) a more extensive use of integrity levels could possibly do the job here.Anonymous
June 12, 2009
at least feel safe and confident that UAC will work as it should. If these UAC issues aren't resolved by RTM, I simply won't be upgrading to 7 and I won't be recommending it to anyone.Anonymous
June 12, 2009
Though acknowledge that you will suddenly have lots of similar items in the same class of "I installed something and it is doing something I didn't think it would do".Anonymous
June 12, 2009
if for no other reason than to get Win 7 off on the right foot. After Vista they could use some good press and rumors of a security problem before launch won't help.Anonymous
June 24, 2009
I have to say I am worried about the possibility for serious computer slowdown. I'm all for a more intensive use of integrity levels.Anonymous
July 06, 2009
As many said before me: Changing UAC Prompting Level should trigger an UAC prompt!Anonymous
July 14, 2009
I am looking forward to the improved UAC - users insist on turning it off too often in Vista.Anonymous
July 29, 2009
i agree. the new and improved UAC will be a whole lot better than the previous oneAnonymous
November 13, 2009
so far i am very impressed with the uac updateAnonymous
November 13, 2009
i hope there are more to come in the futureAnonymous
February 28, 2010
The comment has been removedAnonymous
March 07, 2010
Norton was still making their products compatible with Windows 7 last I checked. I don't believe they've implemented a compatible version of their UAC yet, but the way Windows 7 itself handles it is already somewhat different.Anonymous
March 10, 2010
For all of us working on Windows it is humbling to know that our work affects so many people around the world. The recent feedback is showing us just how much passion people have for Windows!Anonymous
March 10, 2010
There has been no report of a way for malware to make it onto a PC without consent. All of the feedback so far concerns the behavior of UAC once malware has found its way onto the PC and is running.Anonymous
March 29, 2010
The comment has been removedAnonymous
April 07, 2010
"There has been no report of a way for malware to make it onto a PC without consent. All of the feedback so far concerns the behavior of UAC once malware has found its way onto the PC and is running." I think like youAnonymous
May 30, 2010
too bad gamers can not use windows 7Anonymous
March 28, 2011
Innovative & essential concept for all engineers to compete with their struggling program or their accessing program.Actually contrasting idea contain this engineering window 7 is user account control technology which works only security program for Microsoft window.I really want about total internal & conceptual description about this.But going through this blog was quite adventurous for me.<a href="www.briscoweb.com/">web design south carolina</a>Anonymous
December 16, 2011
The comment has been removedAnonymous
July 05, 2015
Good one