View and remediate vulnerabilities for containers running on Kubernetes clusters (risk-based)
Note
This page describes the new risk-based approach to vulnerability management in Microsoft Defender for Cloud. Is you're using the Defender for Cloud Cloud Security Posture Management (CSPM) plan, you should use this method. To use the classic secure score approach, see View and remediate vulnerabilities for images running on your Kubernetes clusters (Secure Score).
Defender for Cloud gives its customers the ability to prioritize the remediation of vulnerabilities containers running on your Kubernetes clusters based on contextual risk analysis of the vulnerabilities in your cloud environment. In this article, we review the Containers running in Azure should have vulnerability findings resolved recommendation. For the other clouds, see the parallel recommendations in Vulnerability assessments for AWS with Microsoft Defender Vulnerability Management and Vulnerability assessments for GCP with Microsoft Defender Vulnerability Management.
To provide findings for the recommendation, Defender for Cloud uses agentless discovery for Kubernetes or the Defender sensor to create a full inventory of your Kubernetes clusters and their workloads and correlates that inventory with the vulnerability reports created for your registry images. The recommendation shows your running containers with the vulnerabilities associated with the images that are used by each container and remediation steps.
Defender for Cloud presents the findings and related information as recommendations, including related information such as remediation steps and relevant CVEs. You can view the identified vulnerabilities for one or more subscriptions, or for a specific resource.
View vulnerabilities for a container
To view vulnerabilities for a container, do the following:
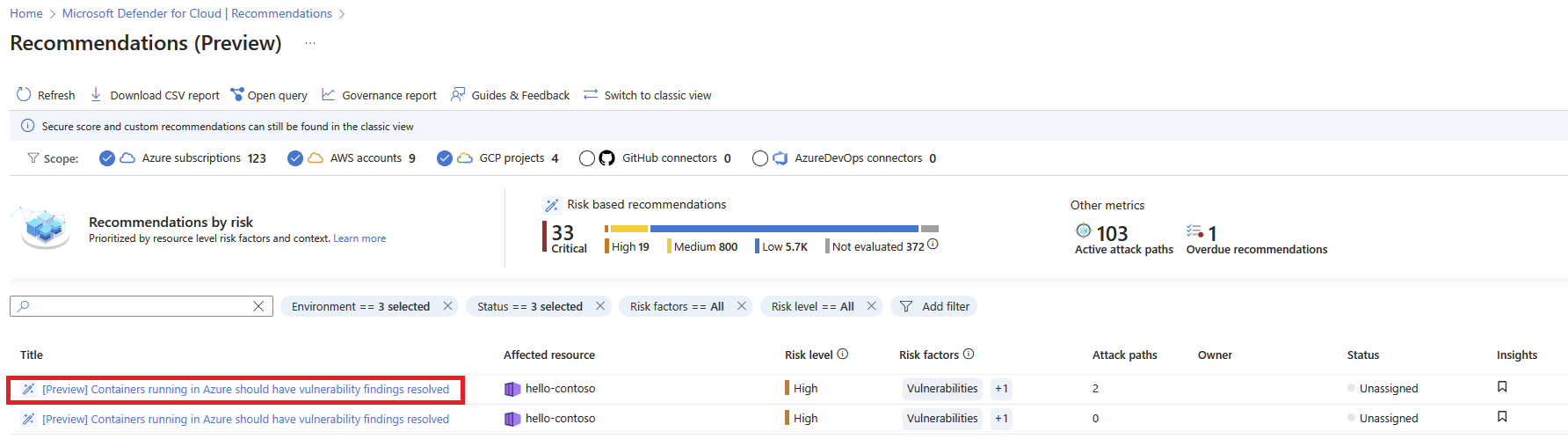
In Defender for Cloud, open the Recommendations page. If you're not on the new risk-based page, select Recommendations by risk on the top menu. If issues were found, you'll see the recommendation Containers running in Azure should have vulnerability findings resolved. Select the recommendation.
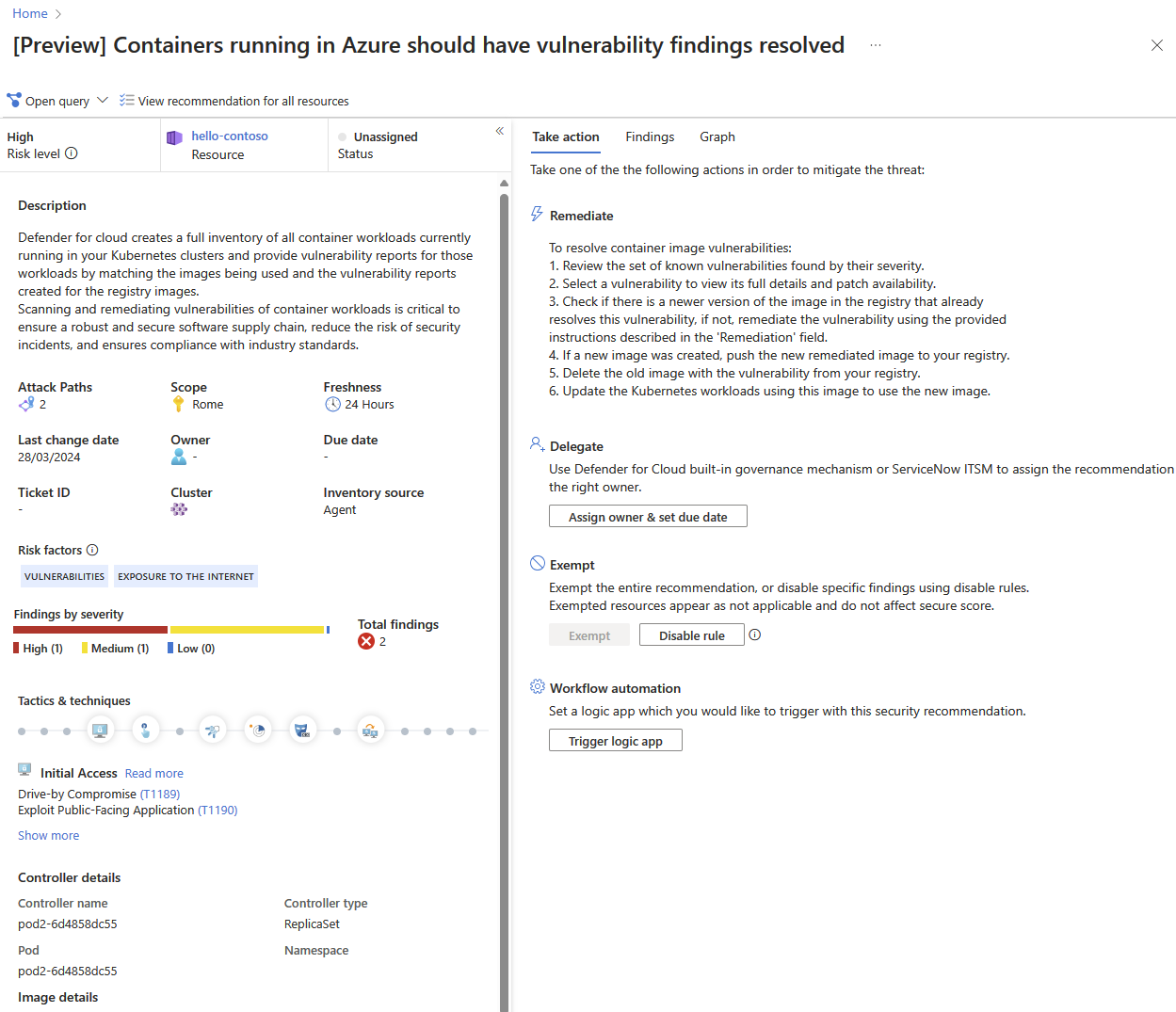
The recommendation details page opens with additional information. This information includes details about your vulnerable container and the remediation steps.
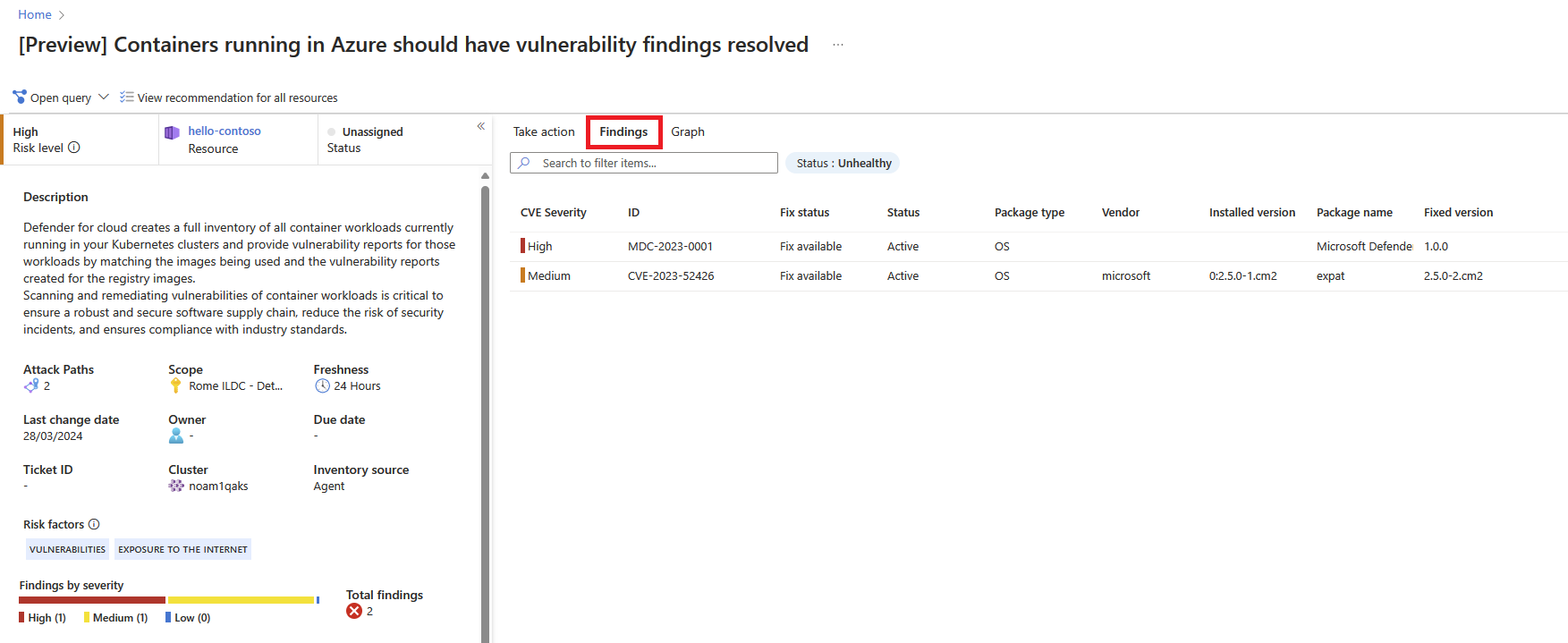
Select the Findings tab to see the list of vulnerabilities impacting the container.
Select each vulnerability for a detailed description of the vulnerability, additional containers affected by that vulnerability, information on the software version that contributes to resolving the vulnerability, and links to external resources to help with patching the vulnerability.
To find all containers impacted by a specific vulnerability, group recommendations by title. For more information, see Group recommendations by title.
For information on how to remediate the vulnerabilities, see Remediate recommendations.
Next step
- Learn how to view and remediate vulnerabilities for registry images.
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for