Restrict Office 365 services to Cloud PCs
Administrators can deny access to Office 365 services on any device other than a Cloud PC. To do so, you can configure Microsoft Entra Conditional Access policies and device filters as described in this article. By following these steps, you can make sure that users use their Cloud PCs as their primary device. In this way, you can improve security for your corporate resources and services.
This article describes how to limit access to Office 365 services. You can use the same strategy with any cloud service that uses Microsoft Entra ID as the authentication source.
Create a Microsoft Entra security group to manage which users are controlled by the new policy. Add to this group all the Cloud PC users who will be subjected to the new policy. Only users in this group will be restricted to using Cloud PCs when accessing Office 365 services. If you want to change a user’s access, you can just remove them from this group.
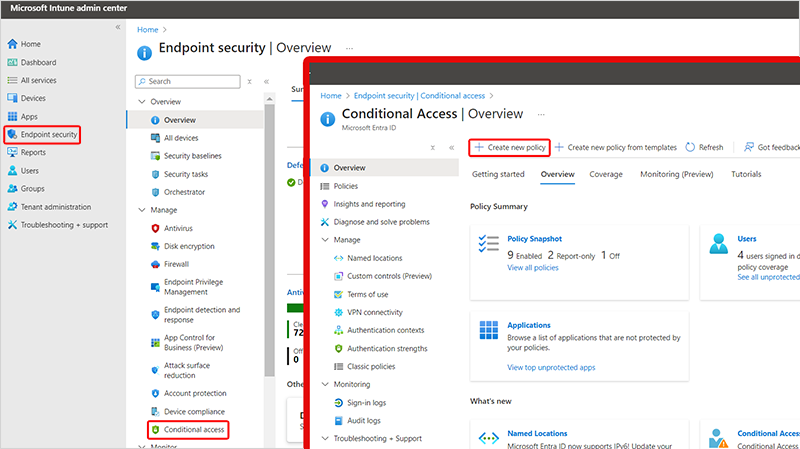
Sign in to Microsoft Intune admin center, select Endpoint security > Conditional Access > Create new policy.
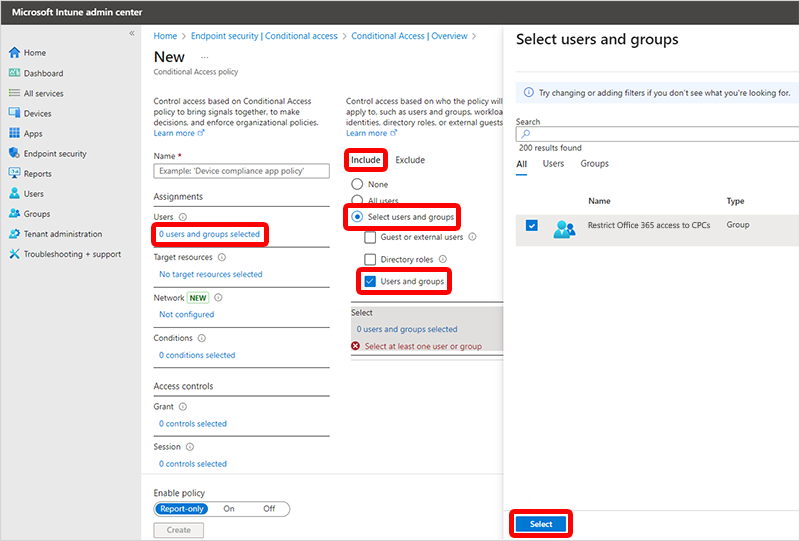
Type a Name for your new Conditional Access policy. For example, “Restrict Office 365 access to CPCs”.
Select 0 users and groups selected > Include > Select users and groups > Users and groups > select the Microsoft Entra security group that you created > Select.
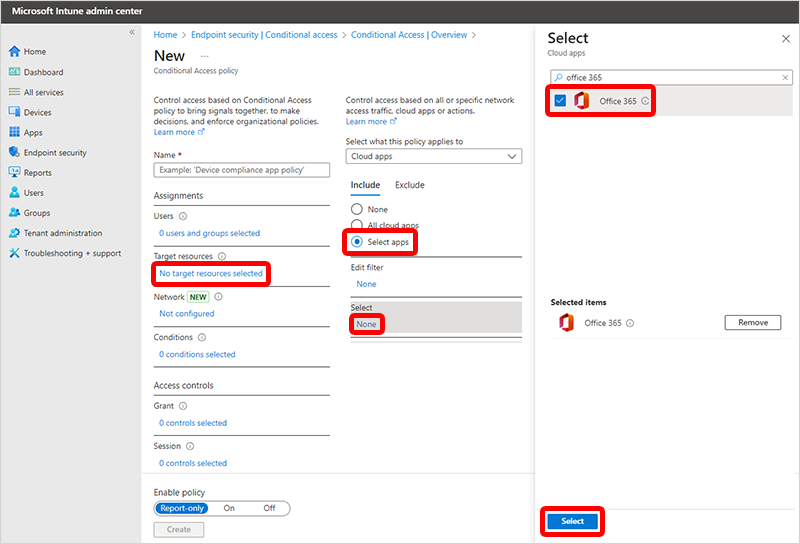
Select No target resources selected > Include > Select apps > None (under Select) > search for and select Office 365 > Select.
Select Exclude > None (under Select excluded cloud apps) > search for and select Azure Virtual Desktop and Windows 365 apps > Select.
Select 0 conditions selected (under Conditions) > Not configured (under Filter for devices).
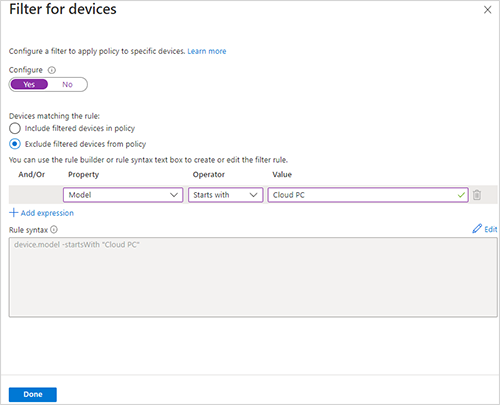
In the Filter for devices pane:
- Set Configure to Yes.
- Select Exclude filtered devices from policy.
- Select the dropdown option under Property > Model.
- Select the dropdown option under Operator > Starts with.
- In the text box under Value, type the value as Cloud PC. If the Cloud PC naming conventions change, change the filter value to match the device names.
- Select Done to set the filter.
You can set more options in this policy as needed, but such additions are outside the scope of this article.
Select 0 controls selected (under Grant) > Block Access >Select.
Select On (under Enable policy). This policy will restrict users from accessing Office 365 services on non-Cloud PC devices. You may want to select Report-only to monitor the policy and build confidence prior to enforcing it.
Select Create to complete the creation of policy.
Note
If you have configured a provisioning policy to Use Microsoft Entra single sign-on, you may need to also add the Microsoft Remote Desktop to the exclude list in Step 6 for single sign-on connections to work as expected.
Other devices
This sample policy can be extended to meet other use cases, like also permitting access to Office 365 services from users' mobile and tablet devices. To do so, make the following changes to the policy:
- On the policy page, select the text under Conditions > Not configured (under Device Platforms).
- Select Yes to turn on the configuration option.
- Select Include > Any device.
- Select Exclude > Android and iOS.
- Select Done to set the filter.
- Select Save.