probably a bit too late to the discussion.
you need to modify the version at the bottom of the vpn xml config file, before ou push it out to devices, from 1 to 2. this instructs the client to force tunnel.
its in the vwan p2s documentation.
This browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
Greetings,
this question relates to the following already existing one: https://video2.skills-academy.com/en-us/answers/questions/589858/azure-wan-and-p2s-vpn-forced-tunneling.html
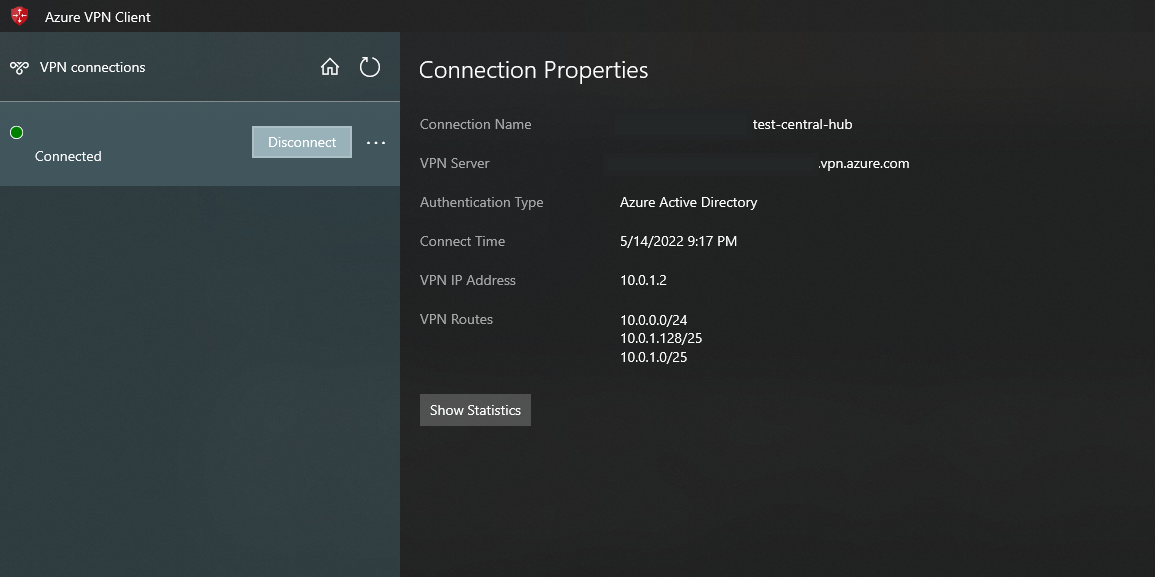
I am facing the same issue: after connecting successfully to the P2S VPN of the virtual hub in the VWAN, my client routing still uses my local adapter and my default ISP's public IP.
The proposed solution of adding the 0.0.0.0/1 and 128.0.0.0/1 routes to the route table of the virtual hub does not work (extensively tested), since for unknown reasons the two routes do not get propagated to the client this way.
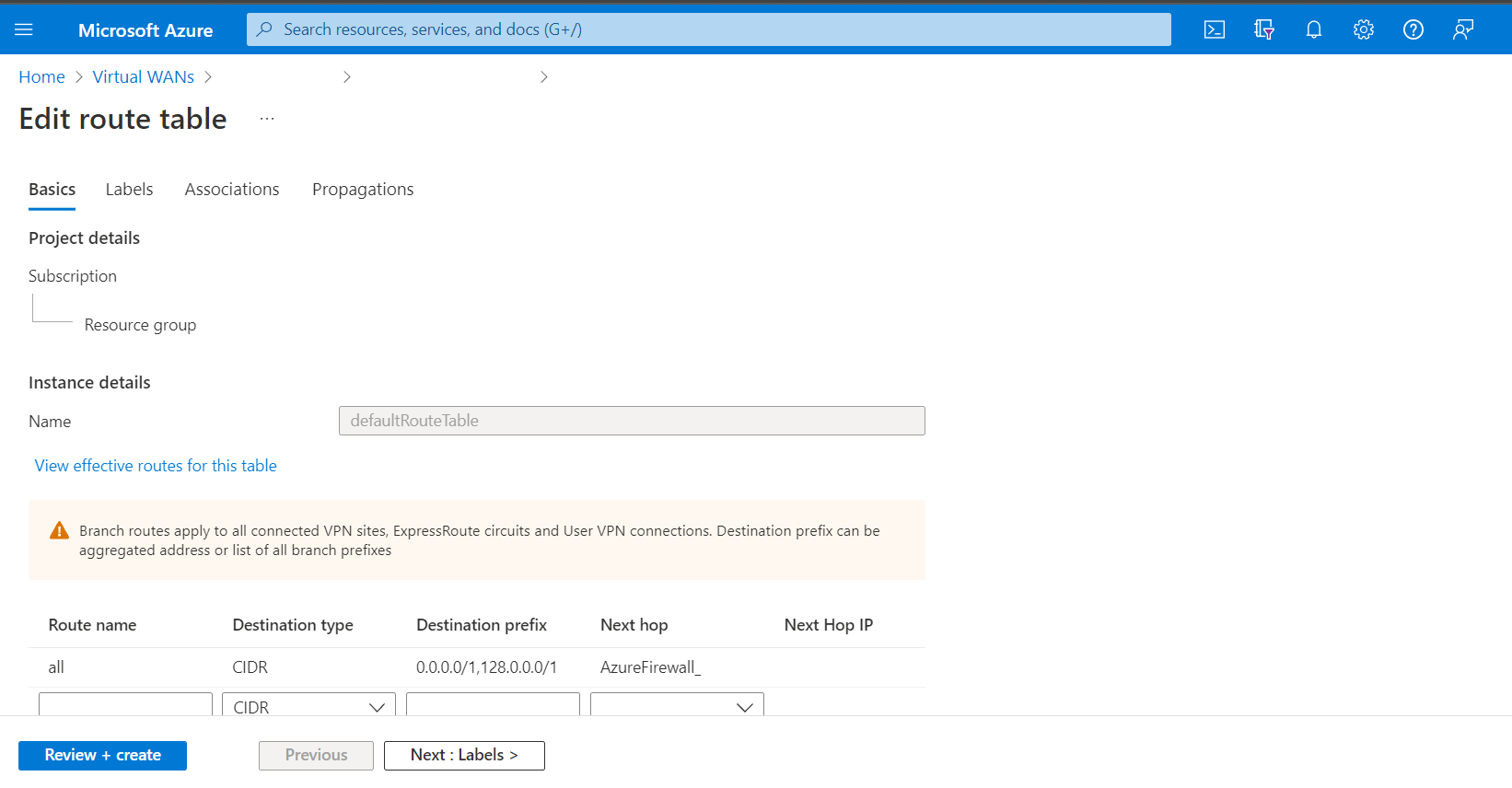
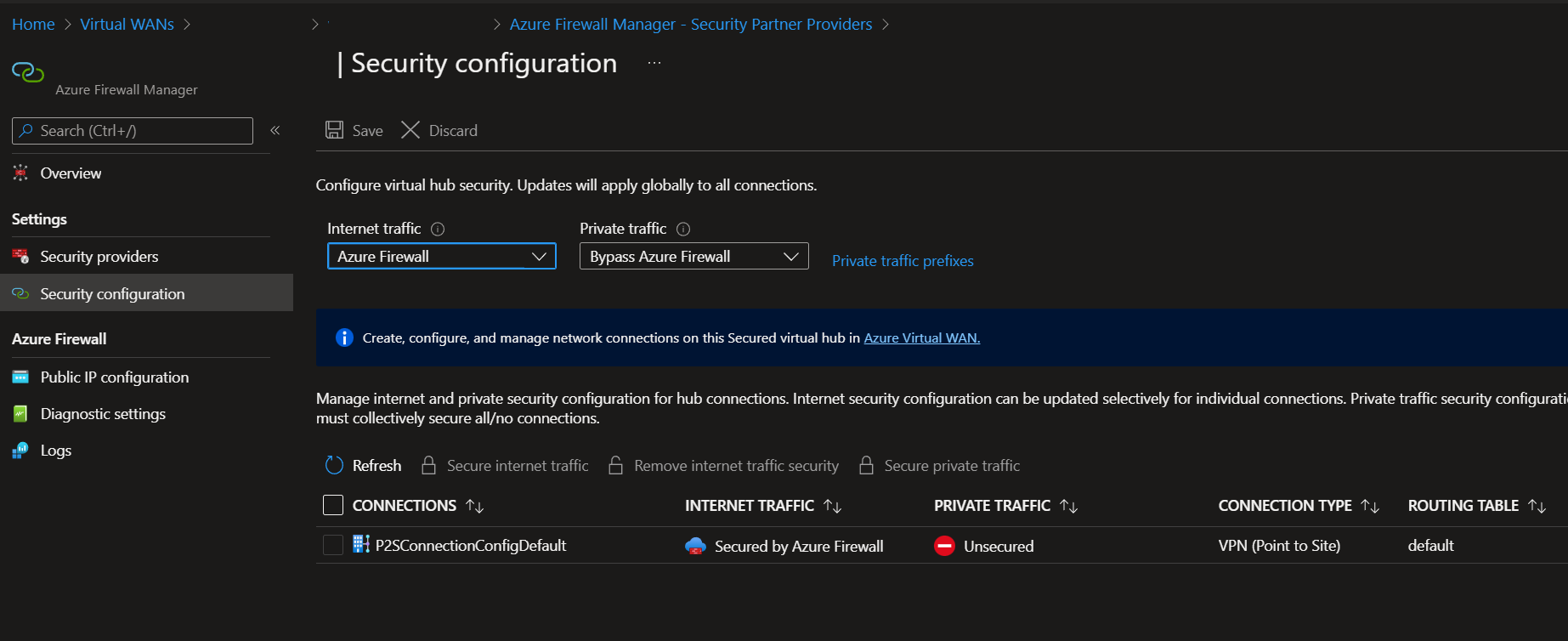
After 'Securing Internet Traffic' through the UI in the Security Configuration of the Firewall, the 0.0.0.0/0 route gets added to the route table and that route does get propagated to the client but it does not force the traffic to use the VPN connection, instead it stays on the local adapter & client ISP public IP.
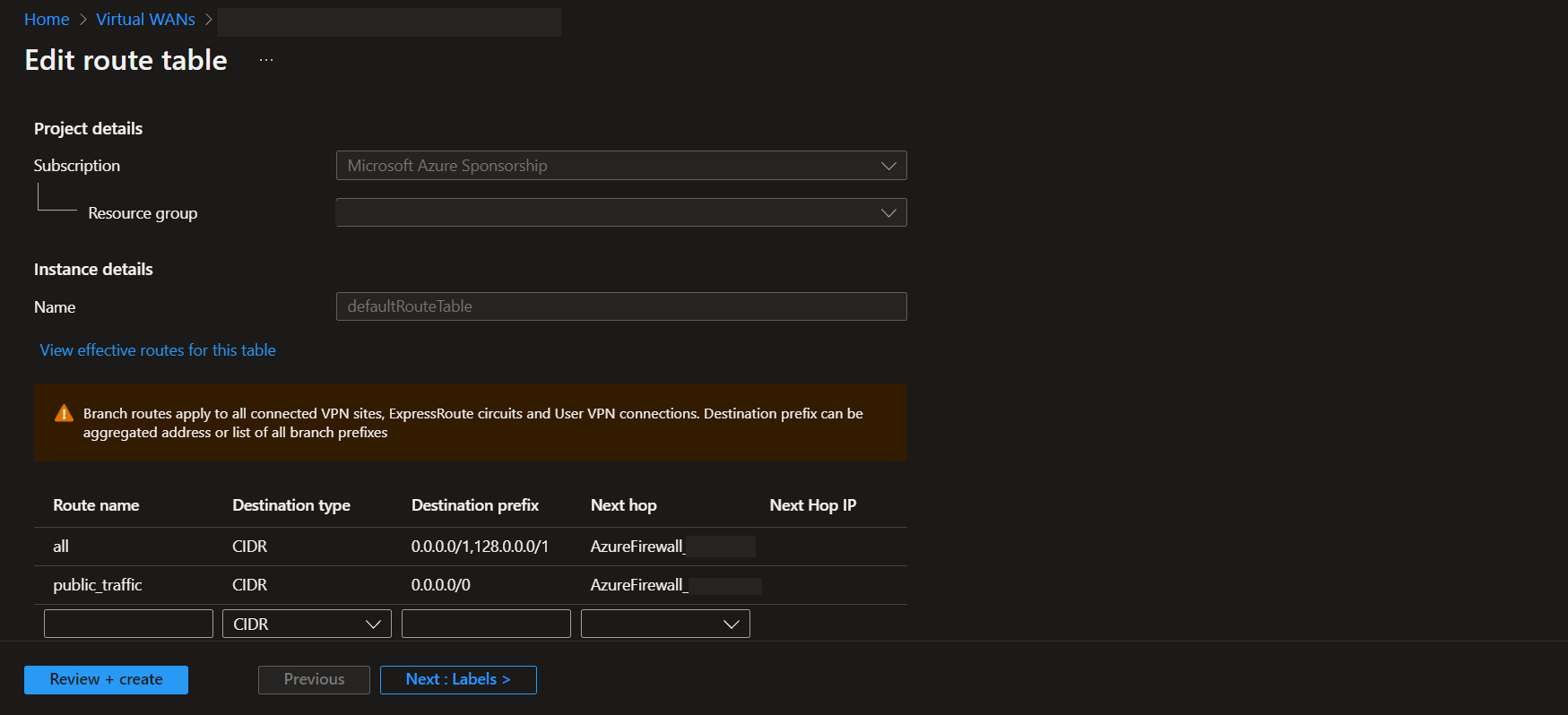
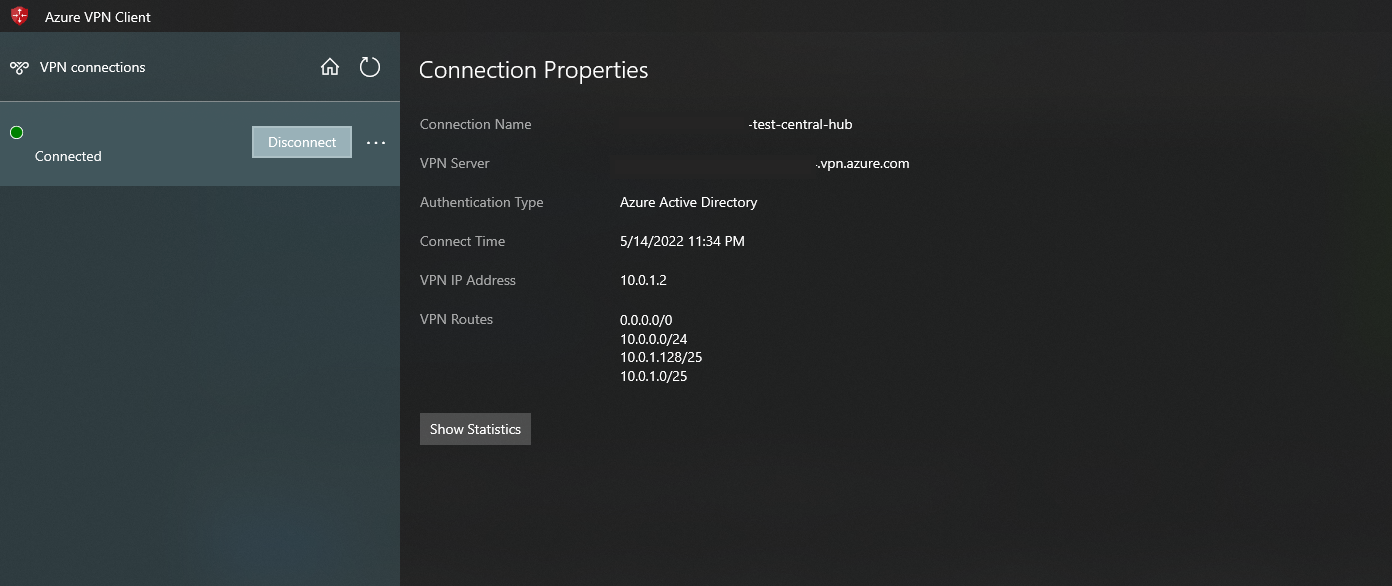
The only workaround that is working is manually editing the azurevpnconfig.xml file and adding the two 0.0.0.0/1 and 128.0.0.0/1 routes there manually. After that the routes show up in the Azure VPN Client and the VWAN Firewall public IP starts to be used. Also one peculiarity here is that tracert and ping (ICMP?) through cmd stop working after this type of configuration.
Is there any proper way to force these two routes to be propagated & advertised to the clients, without a workaround like mentioned above?
This workaround is not acceptable since it moves a central part of configuration away from the central portal and into a simple configuration file which will be distributed and can easily be manually edited.
I suppose this is somewhat of a bug which needs to be adressed by Microsoft.
probably a bit too late to the discussion.
you need to modify the version at the bottom of the vpn xml config file, before ou push it out to devices, from 1 to 2. this instructs the client to force tunnel.
its in the vwan p2s documentation.