Disable basic authentication in App Service deployments
This article shows you how to disable basic authentication (username and password authentication) when deploying code to App Service apps.
App Service provides basic authentication for FTP and WebDeploy clients to connect to it by using deployment credentials. These APIs are great for browsing your site’s file system, uploading drivers and utilities, and deploying with MsBuild. However, enterprises often require more secure deployment methods than basic authentication, such as Microsoft Entra ID authentication (see Authentication types by deployment methods in Azure App Service). Microsoft Entra uses OAuth 2.0 token-based authorization and has many benefits and improvements that help mitigate the issues in basic authentication. For example, OAuth access tokens have a limited usable lifetime, and are specific to the applications and resources for which they're issued, so they can't be reused. Microsoft Entra also lets you deploy from other Azure services using managed identities.
Two different controls for basic authentication are available. Specifically:
- For FTP deployment, basic authentication is controlled by the
basicPublishingCredentialsPolicies/ftpflag (FTP Basic Auth Publishing Credentials option in the portal). - For other deployment methods that use basic authentication, such as Visual Studio, local Git, and GitHub, basic authentication is controlled by the
basicPublishingCredentialsPolicies/scmflag (SCM Basic Auth Publishing Credentials option in the portal).
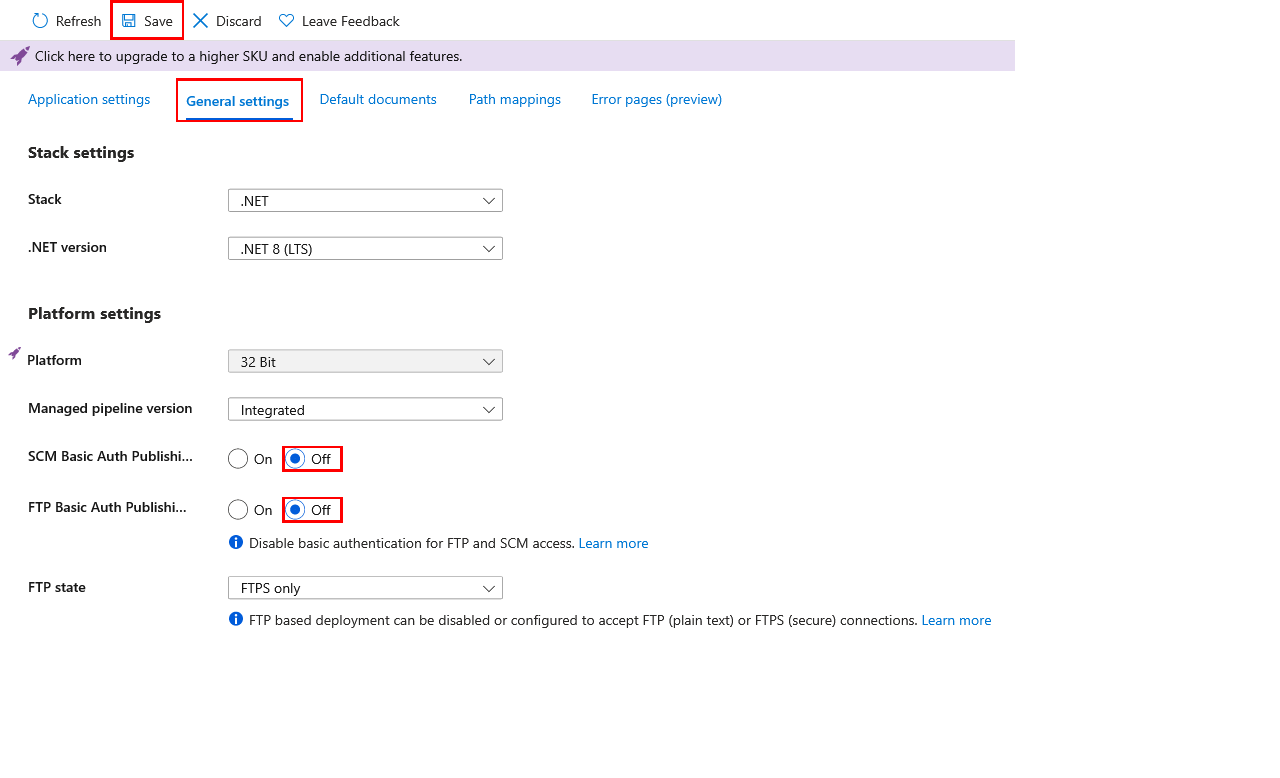
In the Azure portal, search for and select App Services, and then select your app.
In the app's left menu, select Configuration > General settings.
For SCM Basic Auth Publishing Credentials or FTP Basic Auth Publishing Credentials, select Off, then select Save.
To confirm that FTP access is blocked, try connecting to your app using FTP/S. You should get a 401 Unauthenticted message.
To confirm that Git access is blocked, try local Git deployment. You should get an Authentication failed message.
When you disable basic authentication, deployment methods that depend on basic authentication stop working.
The following table shows how various deployment methods behave when basic authentication is disabled, and if there's any fallback mechanism. For more information, see Authentication types by deployment methods in Azure App Service.
| Deployment method | When basic authentication is disabled |
|---|---|
| Visual Studio deployment | Doesn't work. |
| FTP | Doesn't work. |
| Local Git | Doesn't work. |
| Azure CLI | In Azure CLI 2.48.1 or higher, the following commands fall back to Microsoft Entra authentication: - az webapp up - az webapp deploy - az webapp deployment source config-zip - az webapp log deployment show - az webapp log deployment list - az webapp log download - az webapp log tail - az webapp browse - az webapp create-remote-connection - az webapp ssh - az functionapp deploy - az functionapp log deployment list - az functionapp log deployment show - az functionapp deployment source config-zip |
| Maven plugin or Gradle plugin | Works. |
| GitHub with App Service Build Service | Doesn't work. |
| GitHub Actions | - An existing GitHub Actions workflow that uses basic authentication can't authenticate. In the Deployment Center, disconnect the existing GitHub configuration and create a new GitHub Actions configuration with the user-assigned identity option instead. - If the existing GitHub Actions deployment is manually configured, try using a service principal or OpenID Connect instead. - For new GitHub Actions configuration in the Deployment Center, use the user-assigned identity option. |
| Deployment in create wizard | When Basic authentication is set to Disable and Continuous deployment set to Enable, GitHub Actions is configured with the user-assigned identity option (OpenID Connect). |
| Azure Repos with App Service Build Service | Doesn't work. |
| BitBucket | Doesn't work. |
| Azure Pipelines with AzureWebApp task | Works. |
| Azure Pipelines with AzureRmWebAppDeployment task | - Use the latest AzureRmWebAppDeployment task to get fallback behavior. - The Publish Profile ( PublishProfile) connection type doesn't work, because it uses basic authentication. Change the connection type to Azure Resource Manager (AzureRM). - On non-Windows Pipelines agents, authentication works. - On Windows agents, the deployment method used by the task might need to be modified. When Web Deploy is used ( DeploymentType: 'webDeploy') and basic authentication is disabled, the task authenticates with a Microsoft Entra token. There are additional requirements if you're not using the windows-latest agent or if you're using a self-hosted agent. For more information, see I can't Web Deploy to my Azure App Service using Microsoft Entra authentication from my Windows agent.- Other deployment methods work, such as zip deploy or run from package. |
To prevent a lower-priveldged user from enabling basic authentication for any app, you can create a custom role and assign the user to the role.
In the Azure portal, in the top menu, search for and select the subscription you want to create the custom role in.
From the left navigation, select Access Control (IAM) > Add > Add custom role.
Set the Basic tab as you wish, then select Next.
In the Permissions tab, and select Exclude permissions.
Find and select Microsoft Web Apps, then search for the following operations:
Operation Description microsoft.web/sites/basicPublishingCredentialsPolicies/ftpFTP publishing credentials for App Service apps. microsoft.web/sites/basicPublishingCredentialsPolicies/scmSCM publishing credentials for App Service apps. microsoft.web/sites/slots/basicPublishingCredentialsPolicies/ftpFTP publishing credentials for App Service slots. microsoft.web/sites/slots/basicPublishingCredentialsPolicies/scmSCM publishing credentials for App Service slots. Under each of these operations, select the box for Write, then select Add. This step adds the operation as NotActions for the role.
Your Permissions tab should look like the following screenshot:
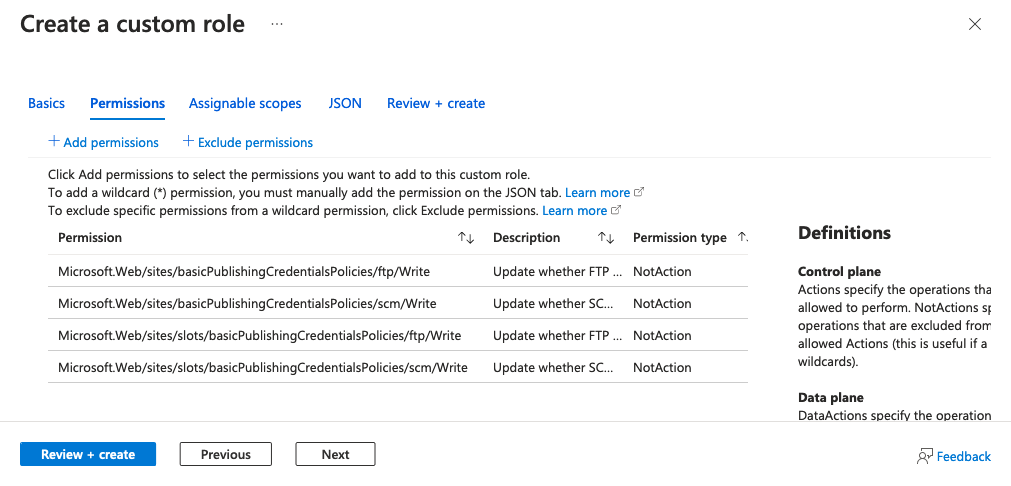
Select Review + create, then select Create.
You can now assign this role to your organization’s users.
For more information, see Create or update Azure custom roles using the Azure portal
All successful and attempted logins are logged to the Azure Monitor AppServiceAuditLogs log type. To audit the attempted and successful logins on FTP and WebDeploy, follow the steps at Send logs to Azure Monitor and enable shipping of the AppServiceAuditLogs log type.
To confirm that the logs are shipped to your selected service(s), try logging in via FTP or WebDeploy. The following example shows a Storage Account log.
{
"time": "2023-10-16T17:42:32.9322528Z",
"ResourceId": "/SUBSCRIPTIONS/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/RESOURCEGROUPS/MYRESOURCEGROUP/PROVIDERS/MICROSOFT.WEB/SITES/MY-DEMO-APP",
"Category": "AppServiceAuditLogs",
"OperationName": "Authorization",
"Properties": {
"User": "$my-demo-app",
"UserDisplayName": "$my-demo-app",
"UserAddress": "24.19.191.170",
"Protocol": "FTP"
}
}
Azure Policy can help you enforce organizational standards and to assess compliance at-scale. You can use Azure Policy to audit for any apps that still use basic authentication, and remediate any noncompliant resources. The following are built-in policies for auditing and remediating basic authentication on App Service:
The following are corresponding policies for slots:
Visual Studio requires basic authentication to deploy to Azure App Service. The warning reminds you that the configuration on your app changed and you can no longer deploy to it. Either you disabled basic authentication on the app yourself, or your organization policy enforces that basic authentication is disabled for App Service apps.