Map Infrastructure as Code templates to cloud resources
Mapping Infrastructure as Code (IaC) templates to cloud resources helps you ensure consistent, secure, and auditable infrastructure provisioning. It supports rapid response to security threats and a security-by-design approach. You can use mapping to discover misconfigurations in runtime resources. Then, remediate at the template level to help ensure no drift and to facilitate deployment via CI/CD methodology.
To set Microsoft Defender for Cloud to map IaC templates to cloud resources, you need:
- An Azure account with Defender for Cloud configured. If you don't already have an Azure account, create one for free.
- An Azure DevOps environment set up in Defender for Cloud.
- Defender Cloud Security Posture Management (CSPM) enabled.
- Azure Pipelines set up to run the Microsoft Security DevOps Azure DevOps extension.
- IaC templates and cloud resources set up with tag support. You can use open-source tools like Yor_trace to automatically tag IaC templates.
- Supported cloud platforms: Microsoft Azure, Amazon Web Services, Google Cloud Platform
- Supported source code management systems: Azure DevOps
- Supported template languages: Azure Resource Manager, Bicep, CloudFormation, Terraform
Note
Microsoft Defender for Cloud uses only the following tags from IaC templates for mapping:
yor_tracemapping_tag
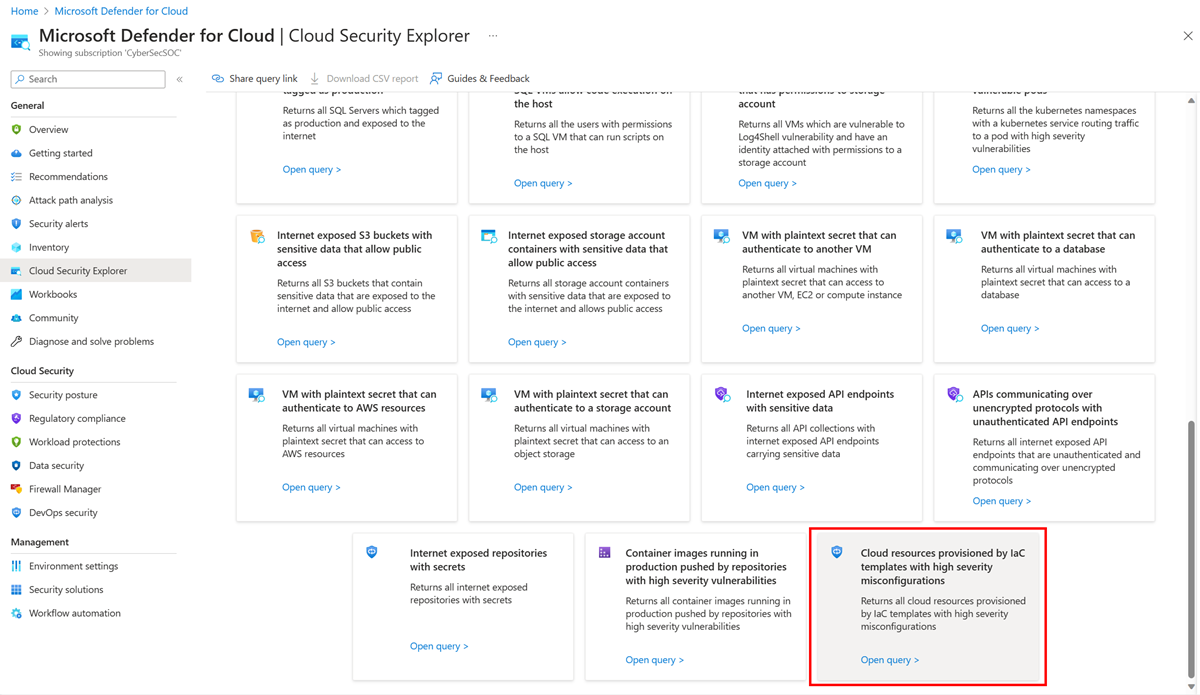
To see the mapping between your IaC template and your cloud resources in Cloud Security Explorer:
Sign in to the Azure portal.
Go to Microsoft Defender for Cloud > Cloud Security Explorer.
In the dropdown menu, search for and select all your cloud resources.
To add more filters to your query, select +.
In the Identity & Access category, add the subfilter Provisioned by.
In the DevOps category, select Code repositories.
After you build your query, select Search to run the query.
Alternatively, select the built-in template Cloud resources provisioned by IaC templates with high severity misconfigurations.
Note
Mapping between your IaC templates and your cloud resources might take up to 12 hours to appear in Cloud Security Explorer.
To create sample IaC mapping tags in your code repositories:
In your repository, add an IaC template that includes tags.
You can start with a sample template.
To commit directly to the main branch or create a new branch for this commit, select Save.
Confirm that you included the Microsoft Security DevOps task in your Azure pipeline.
Verify that pipeline logs show a finding that says An IaC tag(s) was found on this resource. The finding indicates that Defender for Cloud successfully discovered tags.
- Learn more about DevOps security in Defender for Cloud.