Troubleshoot Microsoft Defender XDR service issues
This article addresses issues that might arise as you use the Microsoft Defender XDR service. It provides solutions and workarounds to help you resolve these issues. If you encounter a problem that isn't addressed here, contact Microsoft Support.
If you don't see capabilities on the navigation pane such as the Incidents, Action center, or Hunting in your portal, you need to verify that your tenant has the appropriate licenses.
For more information, see Prerequisites.
If you have Microsoft Defender for Identity deployed in your environment but you're not seeing Defender for Identity alerts as part of Microsoft Defender XDR incidents, you need to ensure that the Microsoft Defender for Cloud Apps and Defender for Identity integration is enabled.
For more information, see Microsoft Defender for Identity integration.
To turn on Microsoft Defender XDR, access Settings from the navigation pane in the Microsoft Defender portal. This navigation item is visible only if you have the prerequisite permissions and licenses.
A false positive is a file or URL that is detected as malicious but isn't a threat. You can create indicators and define exclusions to unblock and allow certain files/URLs. See Address false positives/negatives in Defender for Endpoint.
The Microsoft Defender XDR-ServiceNow connector is no longer available in the Microsoft Defender portal. However, you can still integrate Microsoft Defender XDR with ServiceNow by using the Microsoft Security Graph API. For more information, see Security solution integrations using the Microsoft Graph Security API.
The Microsoft Defender XDR-ServiceNow integration was previously available in the Microsoft Defender portal for preview and feedback. This integration allowed you to create ServiceNow incidents from Microsoft Defender XDR incidents.
In some instances, an administrator block might cause submission issues when you try to submit a potentially infected file to the Microsoft Security intelligence website for analysis. The following process shows how to resolve this problem.
Open your Azure Enterprise application settings. Under Enterprise Applications > Users can consent to apps accessing company data on their behalf, check whether Yes or No is selected.
If No is selected, a Microsoft Entra administrator for the customer tenant needs to provide consent for the organization. Depending on the configuration with Microsoft Entra ID, users might be able to submit a request right from the same dialog box. If there's no option to ask for admin consent, users need to request for these permissions to be added to their Microsoft Entra admin. Go to the following section for more information.
If Yes is selected, ensure the Windows Defender Security Intelligence app setting Enabled for users to sign in? is set to Yes in Azure. If No is selected, you need to request a Microsoft Entra admin enable it.
Important
Microsoft recommends that you use roles with the fewest permissions. This helps improve security for your organization. Global Administrator is a highly privileged role that should be limited to emergency scenarios when you can't use an existing role.
This process requires a Global Administrator or Application Administrator in the tenant.
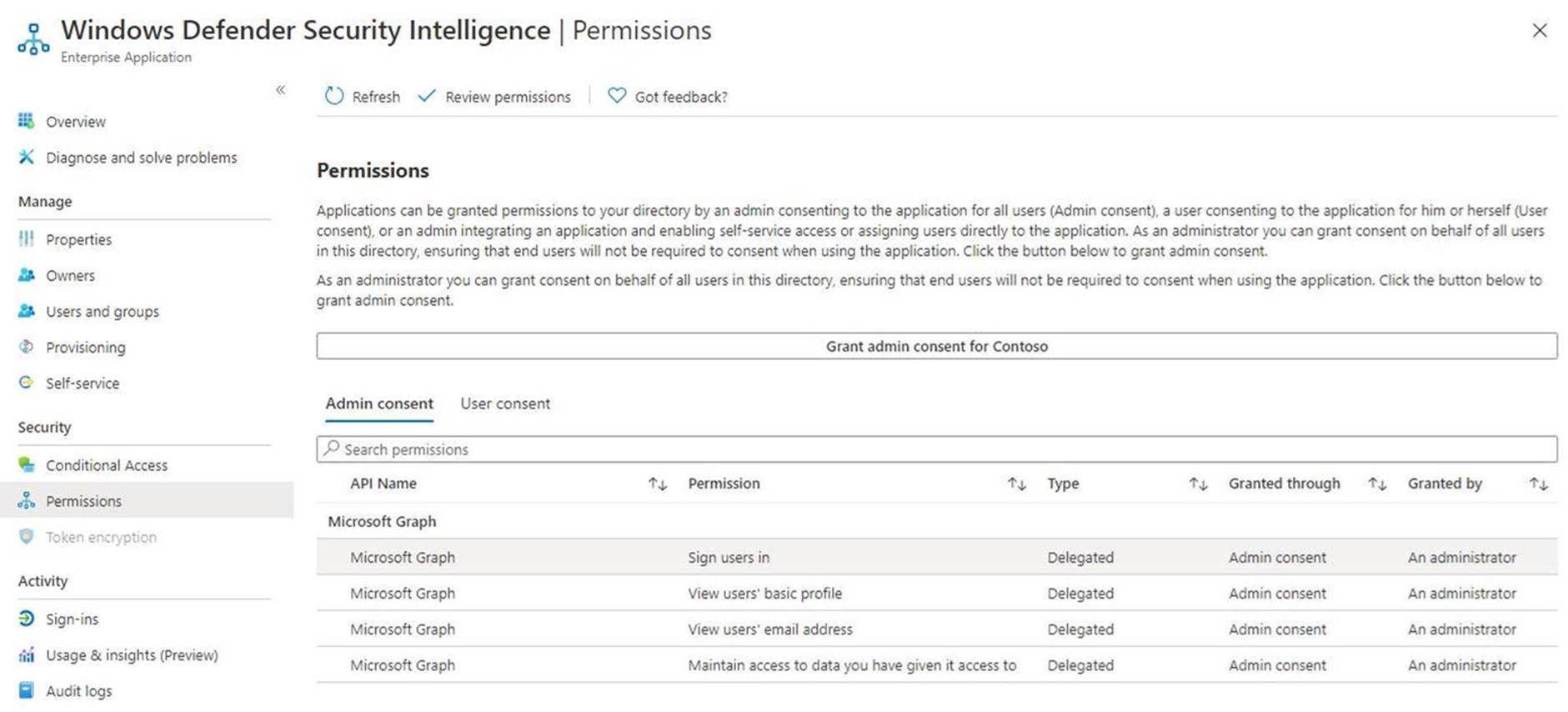
Select Grant admin consent for organization.
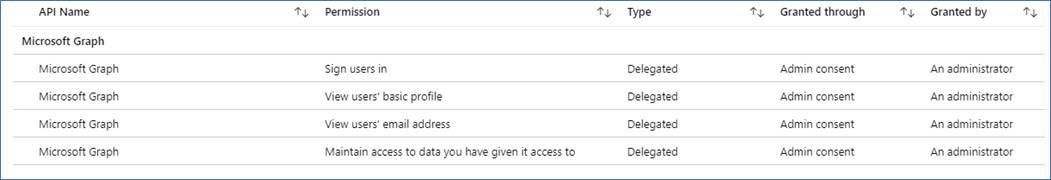
If you're able to do so, review the API permissions required for this application, as the following image shows. Provide consent for the tenant.
If the administrator receives an error while attempting to provide consent manually, try either Option 1 or Option 2 as possible workarounds.
Microsoft Entra Administrators need to allow for users to request admin consent to apps. Verify the setting is configured to Yes in Enterprise applications.
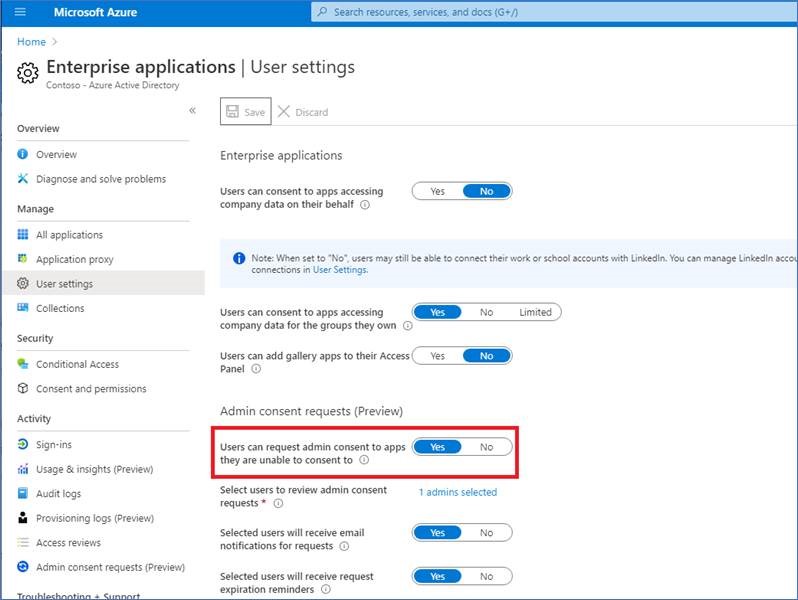
More information is available in Configure Admin consent workflow.
Once this setting is verified, users can go through the enterprise customer sign-in at Microsoft security intelligence, and submit a request for admin consent, including justification.
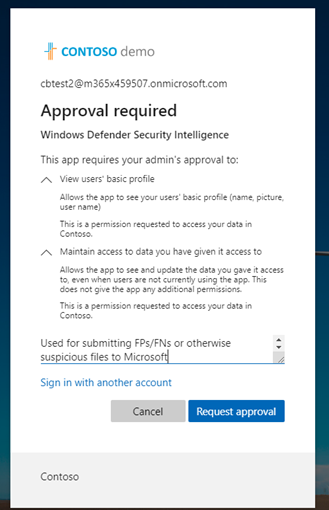
Administrators can review and approve the application permissions Azure admin consent requests.
After providing consent, all users in the tenant will be able to use the application.
This process requires that Global Administrators go through the Enterprise customer sign-in flow at Microsoft security intelligence.
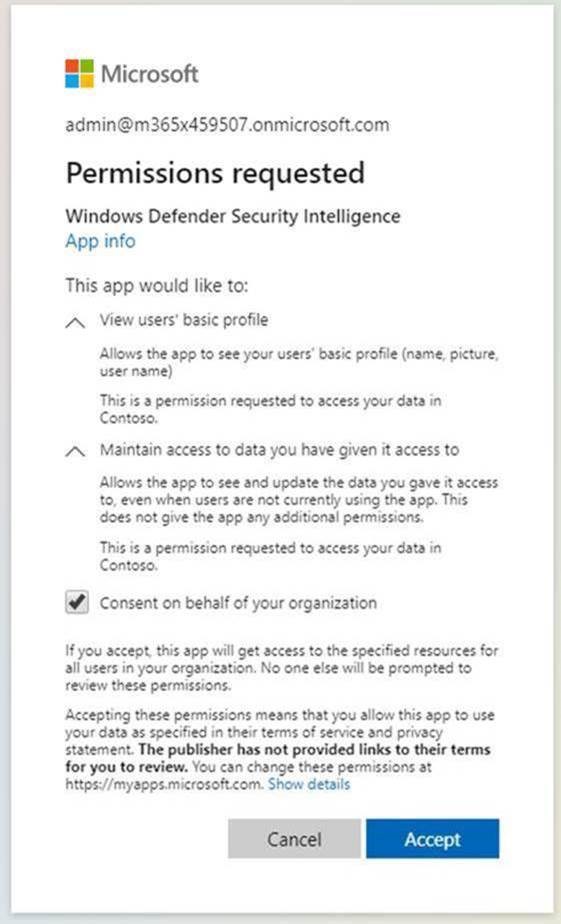
Then, admins review the permissions and make sure to select Consent on behalf of your organization, and then select Accept.
All users in the tenant can now use this application.
If neither of these options resolve the issue, try the following steps (as an admin):
Remove previous configurations for the application. Go to Enterprise applications and select delete.
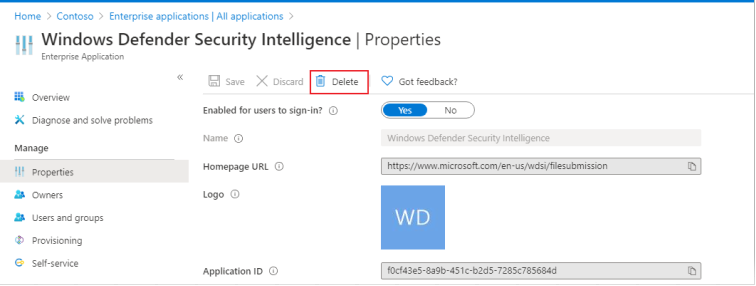
Capture
TenantIDfrom Properties.Replace
{tenant-id}with the specific tenant that needs to grant consent to this application in the URL below. Copy the following URL into browser:https://login.microsoftonline.com/{tenant-id}/v2.0/adminconsent?client_id=f0cf43e5-8a9b-451c-b2d5-7285c785684d&state=12345&redirect_uri=https%3a%2f%2fwww.microsoft.com%2fwdsi%2ffilesubmission&scope=openid+profile+email+offline_accessThe rest of the parameters are already completed.
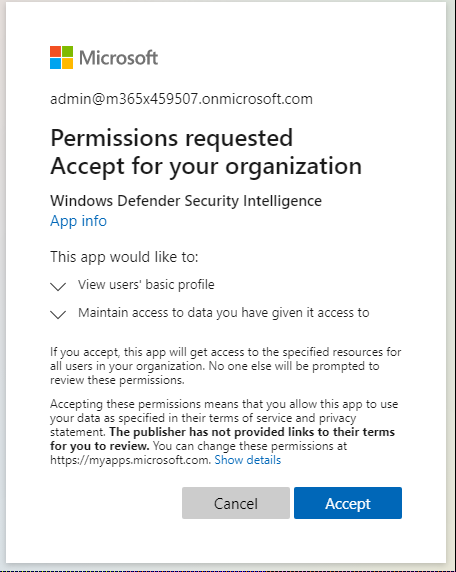
Review the permissions required by the application, and then select Accept.
Confirm the permissions are applied in the Azure portal.
Sign in to Microsoft security intelligence as an enterprise user with a non-admin account to see if you have access.
If the warning isn't resolved after following these troubleshooting steps, call Microsoft support.
Tip
Do you want to learn more? Engage with the Microsoft Security community in our Tech Community: Microsoft Defender XDR Tech Community.