Get started with Data loss prevention policies for Fabric and Power BI
This article describes Microsoft Purview Data Loss Prevention (DLP) policies in Fabric. The target audience is Fabric administrators, security and compliance teams, and Fabric data owners.
To help organizations detect and protect their sensitive data, Fabric supports Microsoft Purview Data Loss Prevention (DLP) polices. When a DLP policy for Fabric detects a supported item type containing sensitive information, a policy tip can be attached to the item that explains the nature of the sensitive content, and an alert can be registered on the data loss prevention Alerts page in the Microsoft Purview portal for monitoring and management by administrators. In addition, email alerts can be sent to administrators and specified users.
This article describes how DLP in Fabric works, lists considerations and limitations as well as licensing and permissions requirements, and explains how DLP CPU usage is metered. For more information, see:
- Respond to a DLP policy violation in Fabric to see how to respond when a policy tip tells you your lakehouse or semantic model has a DLP policy violation.
- Monitor DLP policy violations in Fabric to see how to sign in to the Microsoft Purview portal to see details about DLP violation alerts.
Tipp
Get started with Microsoft Security Copilot to explore new ways to work smarter and faster using the power of AI. Learn more about Microsoft Security Copilot in Microsoft Purview.
- DLP policies for Fabric are defined in the Microsoft Purview portal.
- DLP policies apply to workspaces. Only workspaces hosted in Fabric or Premium capacities are supported. For more information, see Microsoft Fabric concepts and licenses.
- DLP evaluation workloads impact capacity. Currently, DLP for Fabric is available at no additional cost, but this is subject to change. Check this document and the Fabric blog for updates.
- DLP policy templates aren't yet supported for Fabric DLP policies. When creating a DLP policy for Fabric, choose the "custom policy" option.
- Fabric DLP policy rules currently support sensitivity labels and sensitive info types as conditions.
- DLP policies for Fabric aren't supported for sample semantic models, streaming datasets, or semantic models that connect to their data source via DirectQuery or live connection. This includes semantic models with mixed storage, where some of the data comes via import-mode and some comes via DirectQuery.
- DLP policies for Fabric apply only on data in Lakehouse Tables/ folder stored in Delta format.
- DLP policies for Fabric support all the primitive Delta types except timestamp_ntz.
- DLP policies for Fabric aren't supported for the following Delta Parquet data types:
- Binary, timestamp_ntz, Struct, Array, List, Map, Json, Enum, Interval, Void.
- Data with LZ4, Zstd, and Gzip compression codecs.
- Exact data match (EDM) classifiers and trainable classifiers aren't supported by DLP for Fabric. If you select an EDM or trainable classifier in the condition of a policy, the policy will yield no results even if the semantic model or lakehouse does in fact contain data that satisfies the EDM or trainable classifier. Other classifiers specified in the policy will return results, if any.
- DLP policies for Fabric aren't supported in the China North region. See How to find the default region for your organization to learn how to find your organization's default data region.
- Azure capacities aren't supported for DLP in Fabric in the following clusters:
- WUS3
- WUS2
- SCUS
- Onboarding a new tenant to DLP can take a few hours, depending on the number of supported workspaces that are being onboarded.
Before you get started with DLP for Power BI, you should confirm your Microsoft 365 subscription. For full licensing guidance, see Microsoft 365 guidance for security & compliance.
Data from DLP for Fabric can be viewed in Activity explorer. There are four roles that grant permission to Activity explorer; the account you use for accessing the data must be a member of any one of them.
To view the Activity explorer, the account you use for accessing the data must be a member of any of the following roles or above.
- Compliance administrator
- Security administrator
- Compliance data administrator
Wichteg
Microsoft recommends that you use roles with the fewest permissions. This helps improve security for your organization. Global Administrator is a highly privileged role that should only be used in scenarios where a lesser privileged role can't be used.
DLP policies for Fabric currently support (preview) the following item types.
- Semantic models
- Lakehouses
See Considerations and limitations for exceptions.
You define a DLP policy in the data loss prevention section of the Microsoft Purview portal. In the policy, you specify the sensitivity labels and/or sensitive info types you want to detect. You also specify the actions that will happen when the policy detects a semantic model or lakehouse that contains sensitive data of the kind you specified. DLP policies for Fabric support three actions:
User notification via policy tips.
Alerts. Alerts can be sent by email to administrators and users. Additionally, administrators can monitor and manage alerts on the Alerts tab in the Purview portal.
Restrict access. When a supported item type violates a policy configured with the restrict access action, access to the item is restricted, either to the data owners or to members of the organization, depending on how the policy is configured. All other users will lose access to the item.
Notiz
The restrict access action is only enforced on semantic models.
When a semantic model or lakehouse is evaluated by DLP policies, if it matches the conditions specified in a DLP policy, the actions specified in the policy occur. DLP policies are initiated by the following actions:
Semantic models:
A semantic model is evaluated against DLP policies whenever one of the following events occurs:
- Publish
- Republish
- On-demand refresh
- Scheduled refresh
Notiz
DLP evaluation of the semantic model doesn't occur if either of the following is true:
- The initiator of the event (publish, republish, on-demand refresh, scheduled refresh) is an account using service principal authentication.
- The semantic model owner is a service principal.
Lakehouse:
A lakehouse is evaluated against DLP policies When the data within a lakehouse undergoes a change, such as getting new data, connecting a new source, adding or updating existing tables, and more.
When a DLP policy detects an issue with an item:
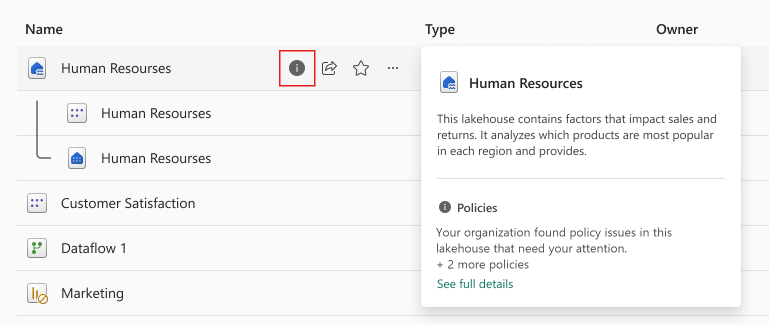
If "user notification" is enabled in the policy, the item will be marked in Fabric with an icon that indicates that a DLP policy has detected an issue with the item. Hover over the icon to display a hover card that provides an option to see the full details in a side panel. For more information about what you see in the side panel, see Respond to a DLP violation in Fabric.
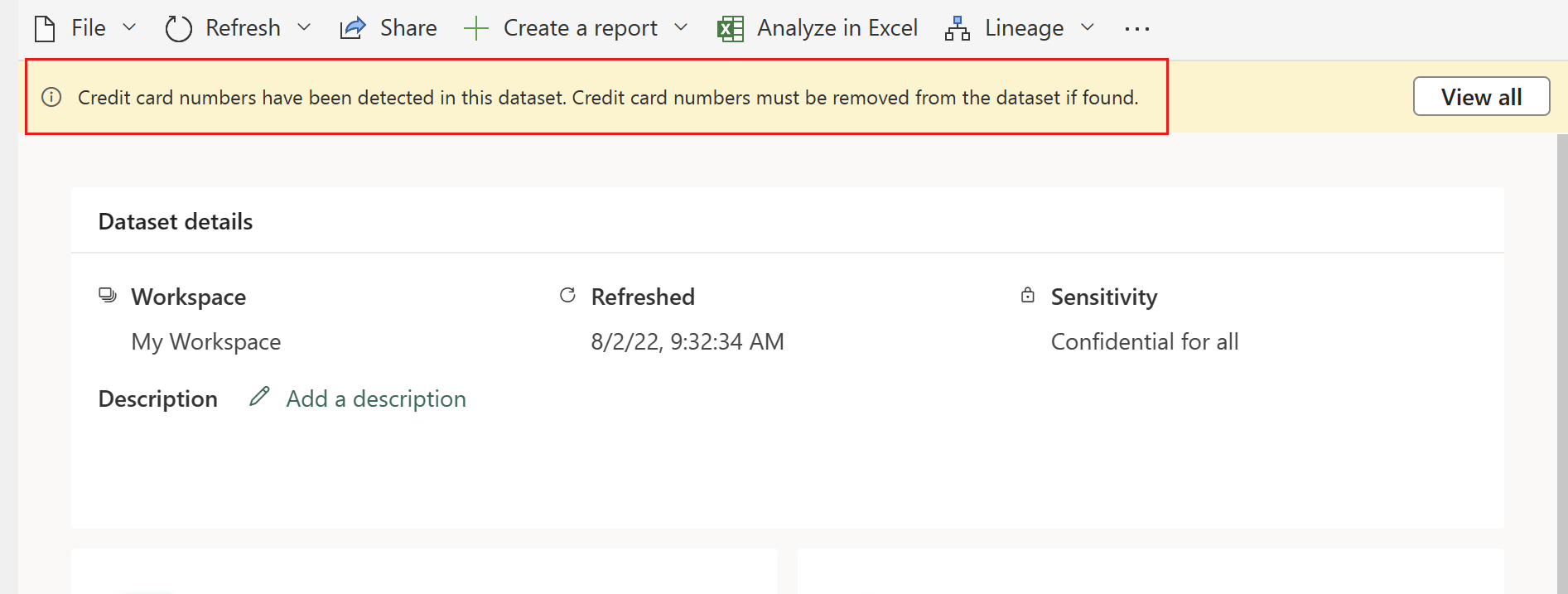
For semantic models, opening the details page will show a policy tip that explains the policy violation and how the type of sensitive information detected should be handled. Selecting View all opens a side panel with all the policy details.
Notiz
If you hide the policy tip, it doesn’t get deleted. It will appear the next time you visit the page.
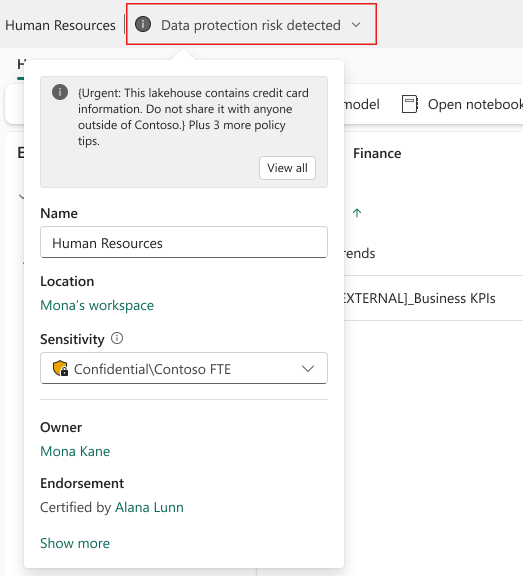
For lakehouses, the indication will appear in the header in edit mode, and opening the fly out makes it possible to see more details about the policy tips affecting the lakehouse. Selecting View all opens a side panel with all the policy details.
If alerts are enabled in the policy, an alert will be recorded on the data loss prevention Alerts page in the Microsoft Purview portal, and (if configured) an email will be sent to administrators and/or specified users. For more information, see Monitor and manage DLP policy violations.
Follow the procedures in Create and Deploy data loss prevention policies and use the custom template.
Wichteg
When you select the locations for your DLP policy for Power BI/Fabric, select only the Power BI/Fabric location. Do not select any other locations, this configuration is not supported.