I also tried the following test-script, it only works when user logging on is local admin:
write-output "Script worked" | out-file C:\Users\[USERNAME_USER_LOGGING_ON]\Desktop\Scripts\output.txt
This browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
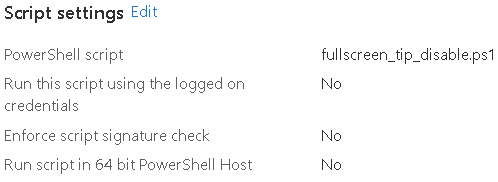
So I added a simple .ps1 script in Intune under Devices, Scripts. It is assigned to a Device-group.
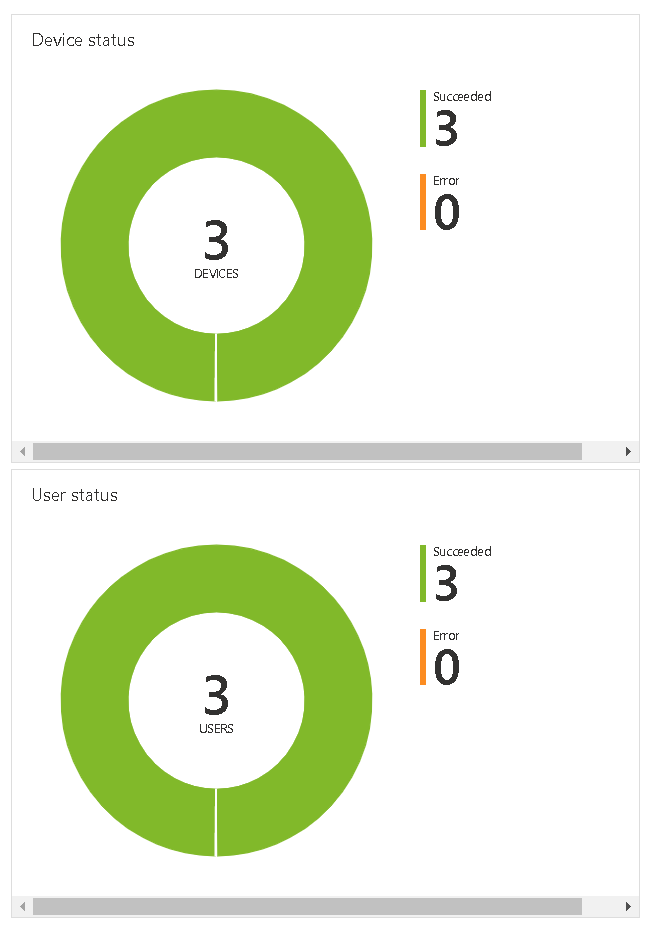
After deploying I can see that the status is showing as Succeeded.
But the script is never executed on the clients. I read that it should be placed in C:\Program Files (x86)\Microsoft Intune Management Extension\Policies\Scripts, but it isn't appearing there.
I tested this script on the client itself and it is working properly (after executing set-executionpolicy remotesigned)
Does anyone know where to start troubleshooting from here?
I also tried the following test-script, it only works when user logging on is local admin:
write-output "Script worked" | out-file C:\Users\[USERNAME_USER_LOGGING_ON]\Desktop\Scripts\output.txt
Does anyone know why this wouldn't work? Is it by design that scripts like this can only be executed when the user logging on is Local Admin?

Have you reviewed the IME log?
The following is to be found in the log about it. Seems to be OK??
[PowerShell] Processing policy with id = 7ce30a5c-5bb9-4d98-84fe-c2eee2ce2876 for user 237ae1b1-87ad-456c-8dca-d7ebb1f6b2d9 IntuneManagementExtension 21-10-2020 08:42:16 11 (0x000B)
[PowerShell] Policy body = New-Item -Path "HKCU:\Software\Citrix\ICA Client\Keyboard Mapping" -Name Tips –Force
New-ItemProperty -Path Registry::"HKEY_CURRENT_USER\Software\Citrix\ICA Client\Keyboard Mapping\Tips" -Name "In full screen mode" -Value 20070313 -PropertyType DWord -Force, hash = fU21F8cYzFkmUSW+GmTZkpTuu9pESxiPXOxfTXBVcQs= IntuneManagementExtension 21-10-2020 08:42:16 11 (0x000B)
[PowerShell] policy hash = fU21F8cYzFkmUSW+GmTZkpTuu9pESxiPXOxfTXBVcQs= IntuneManagementExtension 21-10-2020 08:42:16 11 (0x000B)
[PowerShell] Hash validation pass. IntuneManagementExtension 21-10-2020 08:42:16 11 (0x000B)
set timer, start the timer for workload PowerShell IntuneManagementExtension 21-10-2020 08:42:18 11 (0x000B)
[PowerShell] The policy needs be run as User IntuneManagementExtension 21-10-2020 08:42:18 11 (0x000B)
[PowerShell] After impersonation: DOMAIN\username IntuneManagementExtension 21-10-2020 08:42:18 11 (0x000B)
[PowerShell] configuring ACL for current user IntuneManagementExtension 21-10-2020 08:42:18 11 (0x000B)
PowerShell: Enforce signature check = False IntuneManagementExtension 21-10-2020 08:42:18 11 (0x000B)
PowerShell: Running mode = 1 IntuneManagementExtension 21-10-2020 08:42:18 11 (0x000B)
C:\Program Files (x86)\Microsoft Intune Management Extension\agentexecutor.exe -powershell "C:\Program Files (x86)\Microsoft Intune Management Extension\Policies\Scripts\237ae1b1-87ad-456c-8dca-d7ebb1f6b2d9_7ce30a5c-5bb9-4d98-84fe-c2eee2ce2876.ps1" "C:\Program Files (x86)\Microsoft Intune Management Extension\Policies\Results\237ae1b1-87ad-456c-8dca-d7ebb1f6b2d9_7ce30a5c-5bb9-4d98-84fe-c2eee2ce2876.output" "C:\Program Files (x86)\Microsoft Intune Management Extension\Policies\Results\237ae1b1-87ad-456c-8dca-d7ebb1f6b2d9_7ce30a5c-5bb9-4d98-84fe-c2eee2ce2876.error" "C:\Program Files (x86)\Microsoft Intune Management Extension\Policies\Results\237ae1b1-87ad-456c-8dca-d7ebb1f6b2d9_7ce30a5c-5bb9-4d98-84fe-c2eee2ce2876.timeout" 3600 C:\Windows\System32\WindowsPowerShell\v1.0 0 1 IntuneManagementExtension 21-10-2020 08:42:18 11 (0x000B)
Launch powershell executor in user session IntuneManagementExtension 21-10-2020 08:42:18 11 (0x000B)
[PowerShell] User Id = 237ae1b1-87ad-456c-8dca-d7ebb1f6b2d9, Policy id = 7ce30a5c-5bb9-4d98-84fe-c2eee2ce2876, policy result = Success IntuneManagementExtension 21-10-2020 08:42:23 11 (0x000B)
[PowerShell] Success, Result details length: 0 IntuneManagementExtension 21-10-2020 08:42:23 11 (0x000B)
[PowerShell] cleaned up all inbox files. IntuneManagementExtension 21-10-2020 08:42:23 11 (0x000B)
[PowerShell] reporting policy results ... IntuneManagementExtension 21-10-2020 08:42:23 11 (0x000B)
[PowerShell] Polling thread stopped. IntuneManagementExtension 21-10-2020 08:42:23 5 (0x0005)
Logged on as the same user running the following script (as posted before) just works like it should:

It's clearly running based on the log.
Have you reviewed the contents of C:\Program Files (x86)\Microsoft Intune Management Extension\Policies\Results\237ae1b1-87ad-456c-8dca-d7ebb1f6b2d9_7ce30a5c-5bb9-4d98-84fe-c2eee2ce2876.output (that's the output file based on the log file above so may vary)?
Are you checking the HKCU for the user listed in the log?
Have you tried adding logging to the script?